
A brand new variant of StopCrypt ransomware (aka STOP) was noticed within the wild, using a multi-stage execution course of that includes shellcodes to evade safety instruments.
StopCrypt, also called STOP Djvu, is the most generally distributed ransomware in existence that you simply not often hear about.
Whilst you consistently hear how huge some ransomware operations are, comparable to LockBit, BlackCat, and Clop, you not often hear safety researchers discussing STOP.
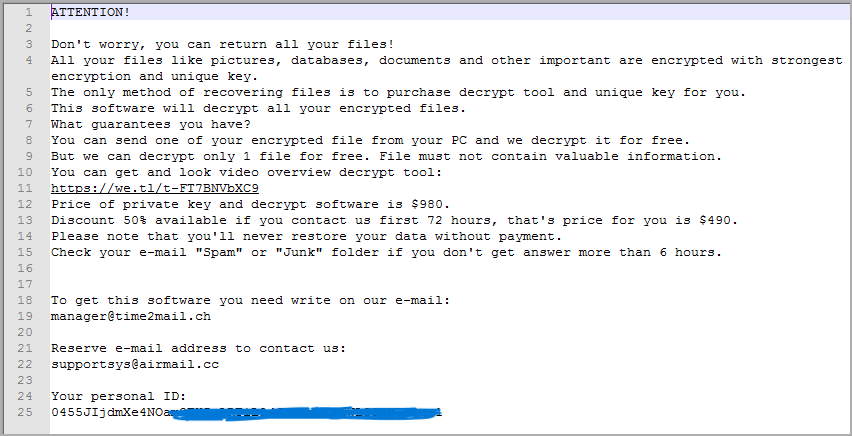
That’s as a result of this ransomware operation doesn’t usually goal companies however quite customers, hoping to generate tens of 1000’s small $400 to $1,000 ransom funds as an alternative of 1 massive multi-million-dollar demand.
The ransomware is often distributed by way of malvertising and shady websites distributing adware bundles disguised as free software program, sport cheats and software program cracks.
Nonetheless, when these applications are put in, the customers turn out to be contaminated with quite a lot of malware, together with password stealing trojans and STOP ransomware.
This leads contaminated customers to desperately attain out to safety researchers, ransomware specialists, and our 807-page STOP ransomware discussion board matter to attempt to obtain assist.
Since its authentic launch in 2018, the ransomware encryptor has not modified a lot, with new variations principally launched to repair vital issues.
For that reason, when a brand new STOP model is launched, it bears watching as a result of massive quantity of people that will probably be affected by it.
New multi-staged execution
SonicWall’s menace analysis staff has uncovered a brand new variant of the STOP ransomware (they name it StopCrypt) within the wild that now makes use of a multi-stage execution mechanism.
Initially, the malware masses a seemingly unrelated DLL file (msim32.dll), presumably as a diversion. It additionally implements a collection of lengthy time-delaying loops which will assist bypass time-related safety measures.
Subsequent, it makes use of dynamically constructed API calls on the stack to allocate the required reminiscence house for learn/write and execution permissions, making detection more durable.
StopCrypt makes use of API requires numerous operations, together with taking snapshots of working processes to grasp the atmosphere during which it is working.
The subsequent stage includes course of hollowing, the place StopCrypt hijacks official processes and injects its payload for discreet execution in reminiscence. That is achieved by means of a collection of fastidiously orchestrated API calls that manipulate course of reminiscence and management circulate.
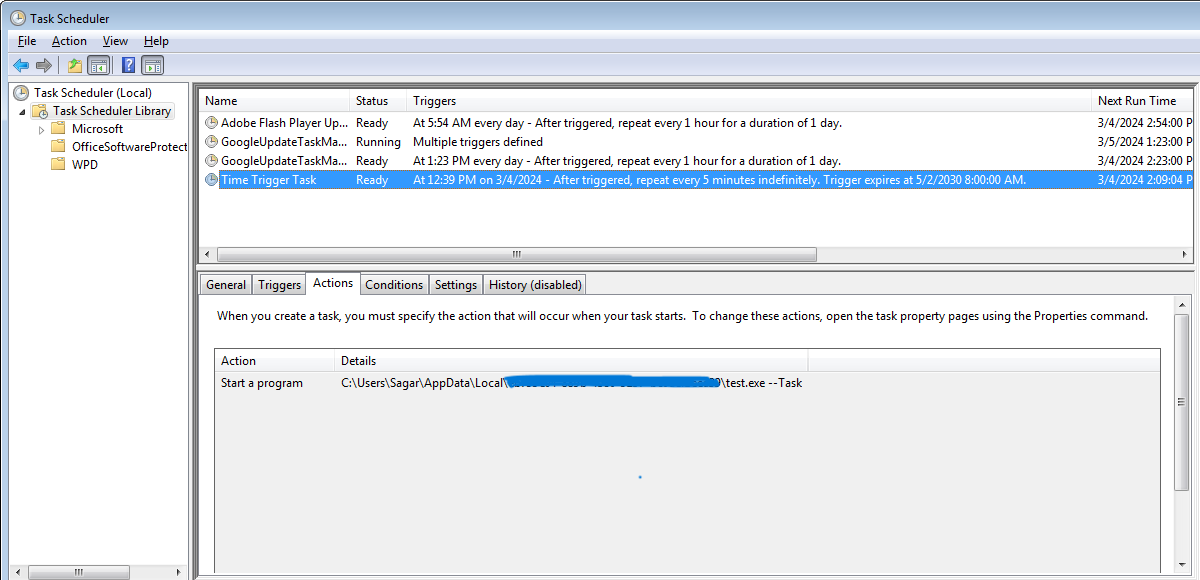
As soon as the ultimate payload is executed, a collection of actions takes place to safe persistence for the ransomware, modify entry management lists (ACLs) to disclaim customers permission to delete vital malware information and directories, and a scheduled job is created to execute the payload each 5 minutes.
Recordsdata are encrypted and a “.msjd” extension is appended to their new names. Nonetheless, it needs to be famous that there are lots of of extensions associated to the STOP ransomware as they alter them typically.
Lastly, a ransom observe named “_readme.txt” is created in each impacted folder, giving victims directions on paying the ransom for information retrieval.
The evolution of StopCrypt right into a extra stealthy and highly effective menace underscores a troubling development in cybercrime.
Although StopCrypt’s financial calls for aren’t excessive and its operators don’t carry out information theft, the injury it may possibly trigger to many individuals might be important.
