
Three cybersecurity researchers found near 19 million plaintext passwords uncovered on the general public web by misconfigured situations of Firebase, a Google platform for internet hosting databases, cloud computing, and app improvement.
The trio scanned greater than 5 million domains and located 916 web sites from organizations that both had no safety guidelines enabled or had set them up incorrectly.
Greater than 125 million delicate person data have been discovered, together with emails, names, passwords, telephone numbers, and billing data with financial institution particulars.
Hundreds of thousands of plaintext passwords uncovered
The researchers (Logykk, xyzeva/Eva, and MrBruh) began trying on the general public internet for personally identifiable data (PII) uncovered by way of weak Firebase situations.
Eva instructed BleepingComputer that they discovered Firebase situations that had no safety guidelines in any respect or have been incorrectly configured and permitted learn entry to databases.
“Many of the websites additionally had write enabled which is unhealthy,” Eva instructed us, including that amongst these in addition they discovered a financial institution.
For every uncovered database, Eva’s script, Catalyst, checked for the kind of knowledge out there and extracted a pattern of 100 data.
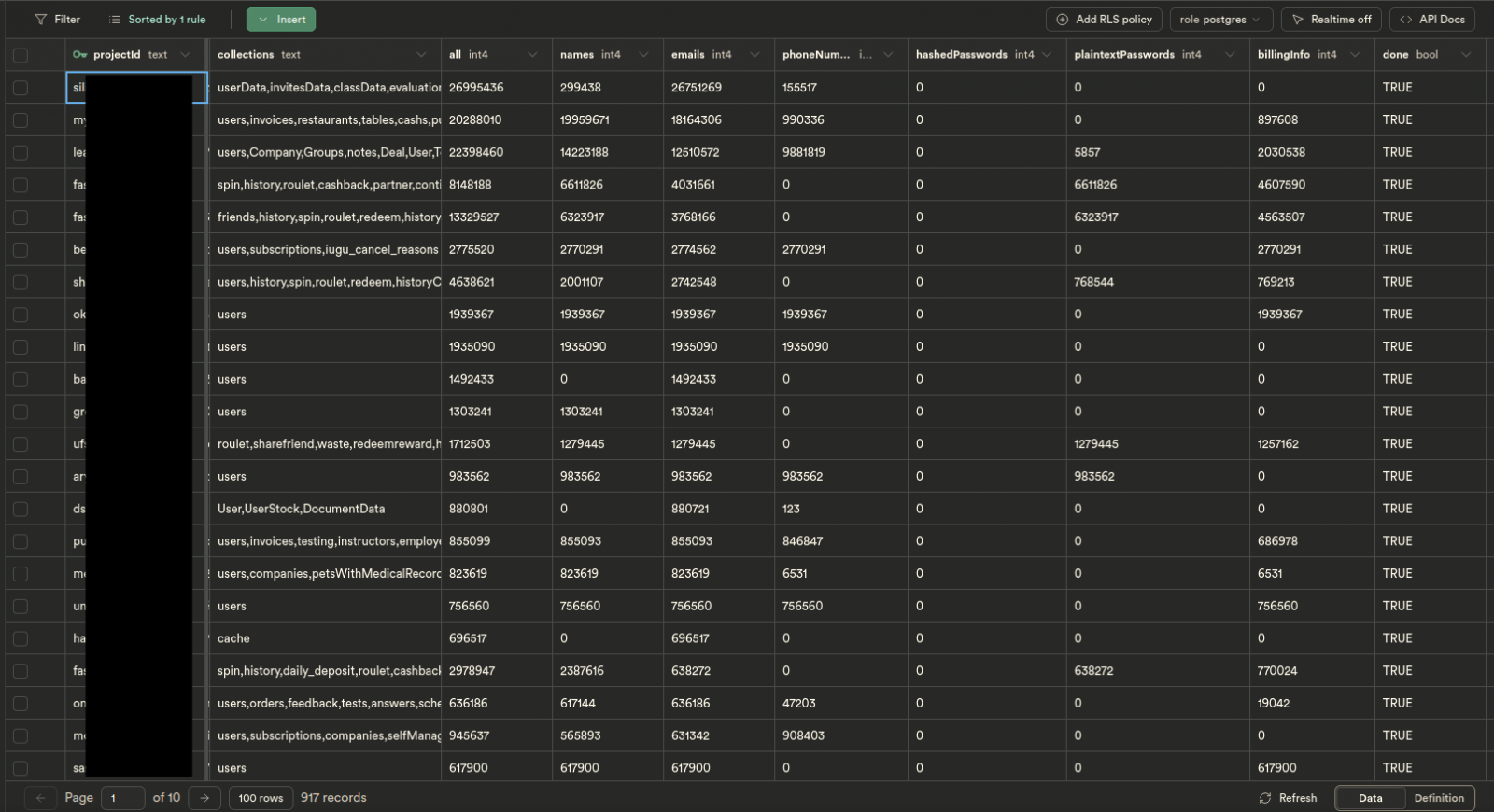
supply: xyzeva
All the main points have been organized in a personal database that gives an outline in numbers of the delicate person data firms expose as a result of improper safety settings:
- Names: 84,221,169
- Emails: 106,266,766
- Cellphone Numbers: 33,559,863
- Passwords: 20,185,831
- Billing Data (Financial institution particulars, invoices, and so forth): 27,487,924
For passwords, the issue will get worse as a result of 98% of them, or 19,867,627 to be precise, are in plain textual content.
Eva instructed us that firms should have gone “out of their strategy to retailer [the password]” in plain textual content as a result of Firebase has an end-to-end id resolution known as Firebase Authentication particularly for safe sign-in processes that don’t expose person passwords within the data.
One strategy to expose person passwords in a Firestore database is for the admin to create a ‘password’ area that shops the info in plaintext.
Alerting website house owners
After analyzing the info from the samples, the researchers tried to warn all impacted firms of improperly secured Firebase situations and despatched 842 emails over 13 days.
Though simply 1% of the positioning house owners replied, 1 / 4 of the notified website directors fastened the misconfiguration of their Firebase platform.
The researchers have been additionally provided bug bounties from two website house owners. Nevertheless, they declined to touch upon the worth of the rewards, saying solely that they accepted them and that they weren’t giant.
Some organizations have been contacted over their buyer help channel however the response was removed from skilled.
Within the case of an Indonesian playing community, that manages 9 web sites, the researchers confronted mockery when reporting the issue and pointing to steering to repair it.
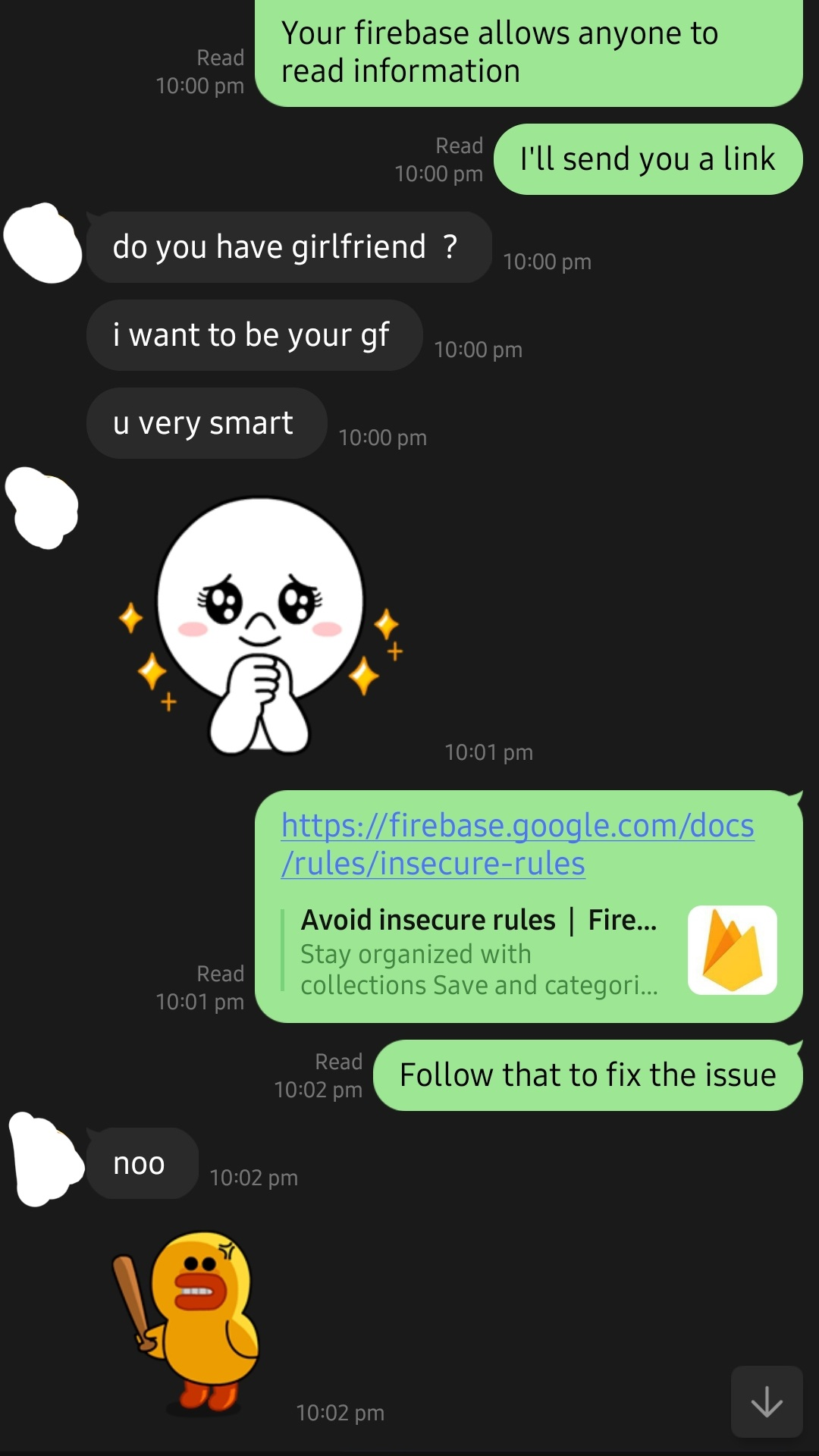
supply: xyzeva
Coincidentally, the identical firm accounted for the biggest variety of uncovered checking account data (8 million) and plain textual content passwords (10 million).
Based on one of many researchers, the corporate is bsed in Indonesia and has an annual revenue of $4 million.
223 million whole uncovered data
Scanning the web, parsing the uncooked knowledge, and organizing took a couple of month and the method didn’t go easily from begin to end.
Initially, they ran the scan utilizing a Python script constructed by MrBruh to verify web sites or their JavaScript bundles for variables in Firebase configurations.
Massive reminiscence consumption made the script unsuitable for the duties and was changed by a variant in Golang written by Logykk, which took greater than two weeks to complete scanning the web.
The brand new script scanned greater than 5 million domains linked to Google’s Firebase platform for backend cloud computing companies and utility improvement.
To automate the verify of learn permissions in Firebase, the staff used one other script from Eva that might crawl the positioning or its JavaScript for entry to Firebase collections (Cloud Firestore NoSQL databases).
The entire variety of data the researchers found in misconfigured databases is 223,172,248. Of those, 124,605,664 data relate to customers; the remainder signify knowledge related to organizations and their checks.
Regardless of the excessive variety of uncovered data, the researchers warn that the determine is conservative and the quantity is probably going bigger.
How it began
Scanning the web for uncovered PII from misconfigured Firebase situations is a follow-up of one other mission the researchers carried out two months in the past, when, as a result of misconfiguration points, they obtained admin after which “superadmin” permissions [1, 2] on an occasion of Firebase utilized by Chattr, an AI-powered hiring software program resolution.
Chattr is utilized by many giant quick meals chains in the USA, comparable to KFC, Wendy’s, Taco Bell, Chick-fil-A, Subway, Arby’s, Applebee’s, and Jimmy John’s, for hiring their workforce.
Whereas the admin position in Chattr’s Firebase dashboard allowed viewing delicate data associated to people attempting to acquire a job in a quick meals chain, the “superadmin” place gave entry to an organization’s account and acted on its behalf for sure duties, together with hiring choices.
The researchers additionally responsibly disclosed the vulnerability to Chattr, who fastened the flaw, however now not responded to additional emails.
