On July 1, 2024, the Qualys Menace Analysis Unit (TRU) disclosed an unauthenticated, distant code execution vulnerability that impacts the OpenSSH server (sshd) in glibc-based Linux techniques.
[For more information visit Qualys Security Advisory and our Cisco Security Advisory on regreSSHion (July 2024).]
Now now we have seen how CVE-2024-6387 has taken the web by storm, making community safety groups scramble to guard the networks whereas app homeowners patch their techniques.
Safe Workload helps organizations get visibility of software workload visitors flows and implement microsegmentation to scale back the assault floor and include lateral motion, mitigating the chance of ransomware.
Under are a number of methods during which Safe Workload might be leveraged to get visibility of affected software workloads and implement segmentation insurance policies to mitigate the chance of workloads being compromised.
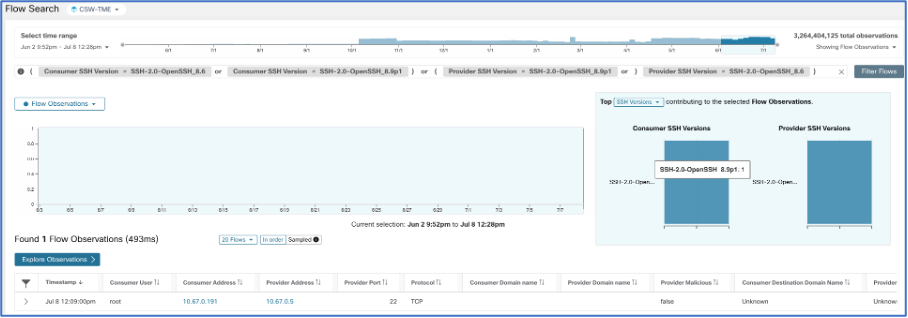
1. Visibility of SSH Visitors Flows
Based on the Qualys Menace Analysis Unit, the variations of OpenSSH affected are these beneath 4.4p1, in addition to variations 8.5p1 by means of 9.8p1, attributable to a regression of CVE-2006-5051 launched in model 8.5p1.
With Safe Workload, it’s simple to seek for visitors flows generated by any given OpenSSH model, permitting us to identify affected workloads immediately and act. Through the use of the next search attributes, we are able to simply spot such communications:
- Shopper SSH Model
- Supplier SSH Model
2. Visibility of OpenSSH Bundle Model in Workloads
Navigate to Workloads > Brokers > Agent Listing and click on on the affected workloads. On the Packages tab, filter for the “openssh” title and it’ll seek for the present OpenSSH bundle put in on the workload.

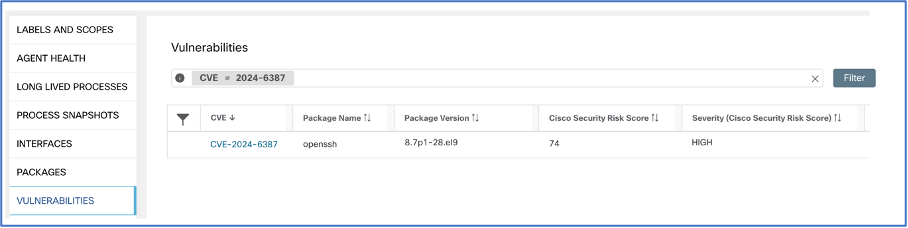
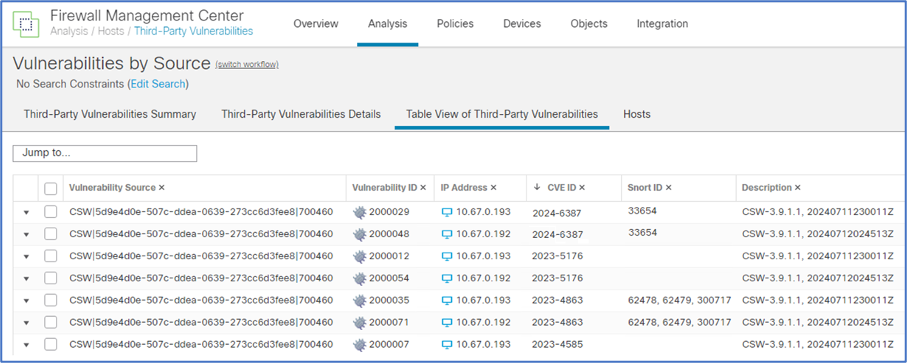
3. Visibility of CVE-ID Vulnerability in Workloads
Navigate to Vulnerabilities tab, and a fast seek for the CVE ID 2024-6387 will search the present vulnerabilities on the workload:
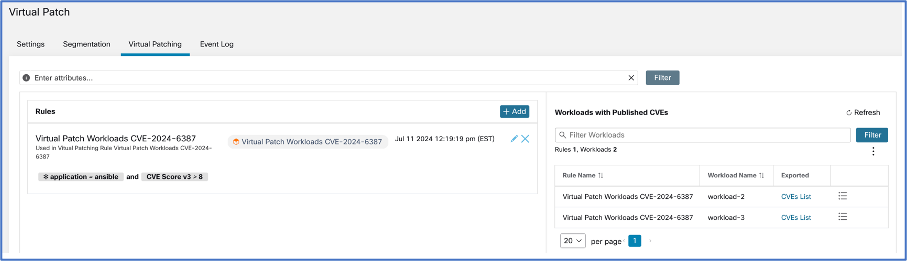
4. Mitigating Danger of regreSSHion
As soon as the related workloads are noticed, there are three fundamental avenues to mitigate the chance: both by microsegmenting the particular software workload, implementing organization-wide auto-quarantine insurance policies to proactively cut back the assault floor, or performing a digital patch with Safe Firewall.
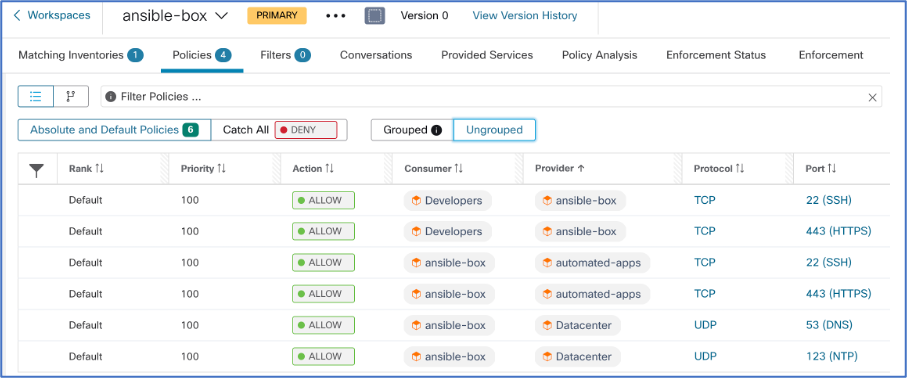
- Microsegmentation: Microsegmentation insurance policies assist you to create fine-grained allow-list insurance policies for software workloads. Which means that solely the desired visitors flows will likely be permitted, denying every other visitors that may be generated from the workload.
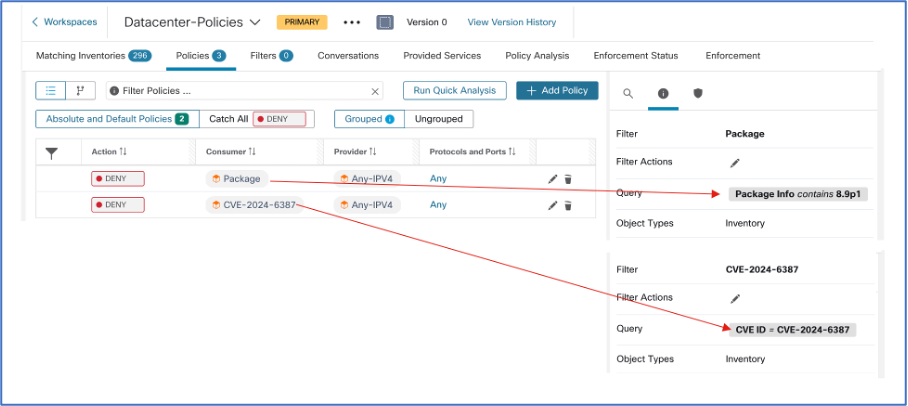
- Auto-Quarantine: You’ll be able to select to implement organization-wide insurance policies to scale back the assault floor by quarantining workloads which have put in a susceptible OpenSSH bundle or are instantly affected by the CVE ID.
- Digital Patch: If quarantining a workload is simply too disruptive to the group (e.g., business-critical functions or internet-exposed functions), you possibly can carry out a digital patch with the assistance of Cisco Safe Firewall to guard the appliance workloads in opposition to the exploit whereas nonetheless sustaining connectivity for the appliance.
5. Course of Anomaly and Change-In Conduct Monitoring of regreSSHion
Even within the state of affairs the place a workload is compromised, Safe Workload gives steady monitoring and anomaly detection capabilities, as proven beneath:
- Course of Snapshot: Offers a course of tree of current runtime processes on the workload. It additionally tracks and maps operating processes to vulnerabilities, privilege escalation occasions, and forensic occasions which have built-in MITRE ATT&CK Methods, Techniques, and Procedures.
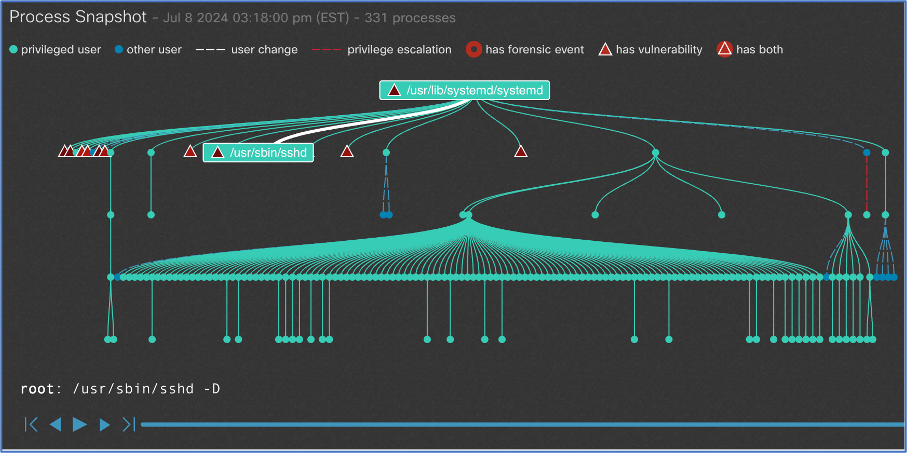
- Forensic Guidelines: Safe Workload comes with 39 out-of-the-box MITRE ATT&CK guidelines to search for methods, ways, and procedures leveraged by adversaries. It is usually doable to create customized forensic guidelines to trace sure course of actions, corresponding to privilege escalation carried out by processes. The system also can generate alerts and ship them to the Safe Workload UI and SIEM techniques.

We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Linked with Cisco Safety on social!
Cisco Safety Social Channels
Share:
