An infostealer malware marketing campaign has collected thousands and thousands of logins from customers of varied gaming web sites, together with gamers that use cheats, pay-to-cheat providers.
The main points emerged after Alexander Wallace, aka ‘PainCorp,’ notified Zebleer, the developer of Phantom Overlay cheats for Name of Obligation and Counter-Strike, about an infostealer database that he had discovered.
“The DB for the stealer represents gaming associated accounts rather more than anything,” Zebleer stated, including that “it is the most important infostealer malware marketing campaign concentrating on players/cheaters in historical past.”
In keeping with the Phantom Overlay developer, the database comprises credentials for a number of million players whose programs had been contaminated in malware marketing campaign.
| Service | Accounts |
| Battlenet | 3,662,647 |
| Activision | 561,183 |
| Elite PVPers | 117,366 |
| UnknownCheats | 572,831 |
| Phantom Overlay | 1,365 |
| BLOG | 67,152 |
| RN | 1,044 |
| ACD | 3,818 |
| AA | 21,564 |
| EO (two domains) | 85,360 |
| Iniuria | 14,181 |
| Gamesense | 18,465 |
The cheat developer additionally notes that the area with the best variety of stolen accounts is Discord, which stands at 14 million entries within the database.
Though it has not been confirmed how the malware was distributed to such numerous customers, Zebleer says that some free or low-cost software program marketed to Name of Obligation players packs an infostealer.
BleepingComputer has reached out to Zebleer for added particulars concerning the database however has not obtained a reply by publishing time.
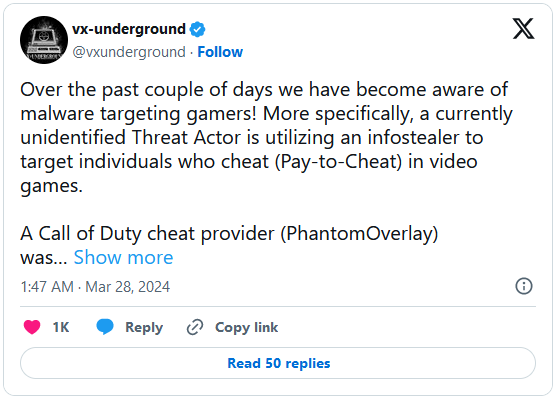
In a separate submit, cybersecurity analysis group vx-underground, says that a number of customers have been reporting that their Electrum BTC wallets had been compromised on account of malware exercise on the pc.
Within the submit, vx-underground says that the gaming discussion board Elite PVPers confirmed that greater than 40,000 legitimate accounts had been compromised.
It seems that the credentials usually are not current in different publicly out there databases with stolen account logins.
Though the variety of logins within the database signifies a big affect on the gaming group, it’s unclear how lots of the accounts are legitimate or duplicates.
Activision Blizzard recommends 2FA
Reportedly, Activision Blizzard is coordinating with cheat builders to restrict the marketing campaign’s affect and supply safety directions to holders of compromised accounts.
BleepingComputer has reached out to Activision Blizzard for a remark and a spokesperson stated that its “servers stay safe and uncompromised.”
“There have been claims that some participant credentials throughout the broader trade might be compromised from malware from downloading or utilizing unauthorized software program. Activision Blizzard servers stay safe and uncompromised,” Activision Blizzard advised BleepingComputer.
“If gamers consider they might have clicked on a suspicious hyperlink or in the event that they wish to guarantee their account is protected, they will change their password and comply with advisable finest practices,” the corporate added, referring to two-factor authentication (2FA).
It’s value mentioning that Activision Blizzard doesn’t have a lot management on the state of affairs as a result of their visibility is restricted so far as the sport assets its gamers use. At this level, the corporate can get a listing of the stolen credentials and drive a password reset an affected accounts.
To make sure the safety of their account and make it tougher for hackers to revenue even when credentials are stolen, customers are advisable to allow two-factor authentication.