Co-authored by Tejas Sheth, Sr. Safety Specialist, Amazon Net Providers – AISPL.
Threat-based Vulnerability Administration (RBVM) represents a strategic method to cyber safety that focuses on figuring out and prioritizing vulnerabilities based mostly on the potential danger they pose to a corporation. This method builds upon conventional vulnerability administration, which regularly includes scanning for and patching all vulnerabilities with out contemplating their precise influence on the enterprise. In RBVM, vulnerabilities are evaluated based mostly on elements just like the criticality of the affected system, the sensitivity of the information concerned, and the chance of exploitation by risk actors. In doing so, organizations can extra successfully prioritize vulnerabilities to deal with the danger the issues most of their environments.
On this weblog, we’ll present you how one can ingest your cloud-specific vulnerability findings from Amazon Inspector into Cisco Vulnerability Administration for a consolidated, risk-based method to successfully deal with vulnerabilities.
First, let’s introduce you to each options and the worth they carry.
Amazon Inspector
Amazon Inspector is a safety evaluation service designed to assist AWS prospects enhance the safety and compliance of their purposes deployed on AWS. It robotically assesses purposes for vulnerabilities or deviations from greatest practices. After performing an evaluation, Amazon Inspector produces an in depth checklist of safety findings prioritized by degree of severity. These findings might be built-in with different companies for in-depth vulnerability evaluation and administration, enabling AWS customers to take actionable steps in direction of remedying potential safety points.
Amazon Inspector calculates its distinctive Inspector Rating based mostly on a wide range of elements past the Widespread Vulnerability Scoring System (CVSS). This consists of assessing whether or not the community is reachable from the web, the CVSS rating itself, and different proprietary parameters. which supplies a numerical rating reflecting the severity of a vulnerability based mostly on its intrinsic qualities, the Inspector Rating additionally considers the context of the AWS setting to prioritize points extra successfully.
Particulars supplied by Amazon Inspector embody:
- Mapping of findings to MITRE ATT&CK methods (TTPs),
- Proof particulars,
- Data on identified malware,
- References to CISA advisories,
- Sources affected,
- Remediation steps, and
- Affected packages.

Amazon Inspector additionally helps the export of Software program Invoice of Supplies (SBOM), CIS (Heart for Web Safety) benchmark scanning for EC2 cases, and gives scanning capabilities for AWS Lambda, container pictures in Amazon Elastic Container Registry (ECR), and Amazon EC2 cases with out the necessity for agent set up or guide intervention, enhancing the safety posture with minimal overhead.
Cisco Vulnerability Administration
Cisco Vulnerability Administration, a risk-based vulnerability administration SaaS answer, prioritizes vulnerabilities that pose an actual danger, enabling Safety and IT groups to focus their restricted sources on what issues most for environment friendly remediation and danger discount. With danger scoring powered by information science—machine studying and patented approaches to predictive modeling—Cisco’s prioritization evaluates each enterprise information and a wealth of knowledge on real-world exploit exercise after which interprets that context into actionable intelligence to information remediation selections and useful resource allocation. Information from instruments like Amazon Inspector might be simply ingested into Cisco Vulnerability Administration for a holistic method to risk-based prioritization.

Cisco Vulnerability Administration makes use of risk and exploit intelligence from 19+ feeds, together with Cisco Talos, and makes use of the one dataset on quantity and velocity of exploitation within the wild. These information sources construct a machine studying mannequin for vulnerability danger. This mannequin is then mixed with asset criticality that may be pulled robotically from a CMDB or manually inputted by a consumer, the asset’s place within the community, and the patch degree aggregation to offer suggestions, danger assessments, and measure danger over time on the vulnerability, asset, and group of belongings degree.
Utilizing the Amazon Inspector Toolkit Connector for Cisco Vulnerability Administration
When Amazon Inspector asset and vulnerability information is ingested into Cisco Vulnerability Administration, it enhances the vulnerability administration course of by integrating cloud-specific safety insights right into a broader vulnerability administration technique. By this integration, organizations can benefit from:
- Information Aggregation: Amazon Inspector’s findings, which embody recognized vulnerabilities and their particulars, are imported into Cisco Vulnerability Administration. This course of consolidates information from numerous sources, together with cloud environments, offering a unified view of safety vulnerabilities throughout the group’s infrastructure.
- Threat Evaluation and Prioritization: Cisco Vulnerability Administration applies its risk-based vulnerability prioritization method to the ingested information from Amazon Inspector and different sources. This implies it assesses and prioritizes vulnerabilities based mostly on numerous elements such because the severity of the vulnerability, the exploitability, the criticality of the affected asset, and the presence of identified exploits within the wild. This prioritization helps in focusing remediation efforts the place they’re most wanted.
- Actionable Insights and Remediation Steering: Cisco Vulnerability Administration gives actionable insights and steerage on methods to remediate recognized vulnerabilities. It supplies context and intelligence that helps safety groups perceive the potential influence on every vulnerability and the very best steps to mitigate them.
Guided Steps on Configuring the Integration
The Amazon Inspector toolkit is a set of capabilities for information and API scripts you need to use with the Cisco Vulnerability Administration platform. It’s organized into duties—models of performance that may be referred to as and used from the command line.
Step 1
Pull the newest picture out there on Docker Hub. See Operating The Newest Picture part for precise set of instructions to carry out this process.
Step 2
To herald asset and vulnerability information from Amazon Inspector, begin by operating the Docker picture with AWS Inspector as process and offering the right AWS authentication technique. This integration helps a number of sorts of authentication strategies supplied by AWS SDK. You’ll find the checklist of supported authentication strategies below AWS Authentication.
The under command is an instance of operating the Docker picture with process as AWS_inspector2 and utilizing IAM roles for authentication:
docker run -v ~/.aws:/root/.aws –env AWS_REGION=us-east-1 –env AWS_PROFILE=inspector_test –rm -it toolkit:newest
process=aws_inspector2 aws_role_arn=””arn:aws:iam::123456789012:function/Inspectorv2ReadOnly””
Step 3
Click on the Information Importer connector below the Connectors tab in Cisco Vulnerability Administration:

Create the connector by including a Title and Asset Inactivity Restrict and click on Save:

Step 4
When you depart off the Cisco Vulnerability Administration (previously Kenna) API Key and Connector ID in step 2, the duty will create a JSON file within the default or specified output listing. You possibly can add the JSON file manually to the connector created on the UI in Step 3 to confirm the ensuing information and diagnose any points with the JSON file.
Step 5
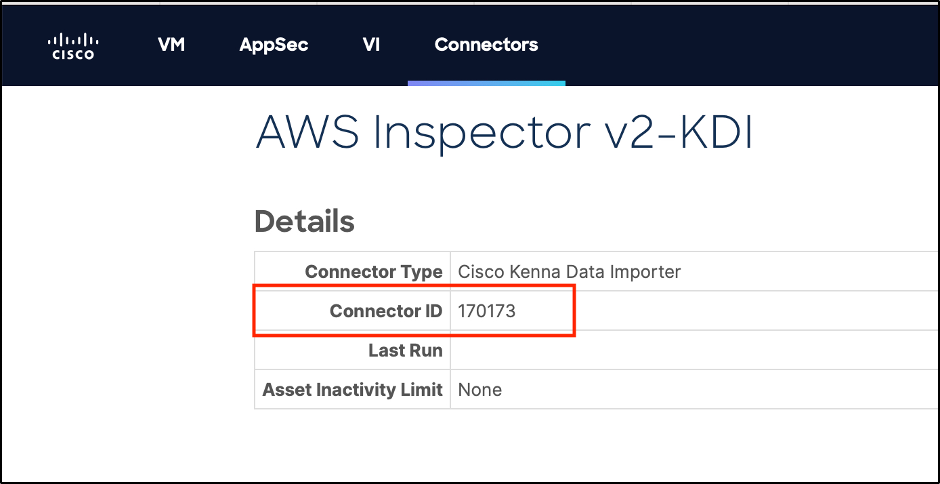
Click on into the newly created Connector and report the Connector ID (this Connector ID is required for Step 7):
Step 6
In earlier steps, we manually uploaded the JSON file on Cisco Vulnerability Administration. Now, we will automate this course of by the Command line utilizing Cisco Vulnerability Administration API Key and Connector ID. To generate an API Key, comply with these steps.
Step 7
Run the duty along with your Cisco Vulnerability Administration (previously Kenna) API Key & Connector ID (IAM function authentication is used within the command under).
docker run -v ~/.aws:/root/.aws –env AWS_REGION=us-east-1 –env AWS_PROFILE=inspector_test –rm -it toolkit:newest
process=aws_inspector2 kenna_api_key=$KENNA_API_KEY kenna_connector_id=12345 aws_role_arn=””arn:aws:iam::123456789012:function/Inspectorv2ReadOnly””
For extra particulars, try this connector process on GitHub. Observe: The duty at the moment solely handles package deal vulnerabilities, not code vulnerabilities (in AWS Lambda) or community reachability findings. Suppressed findings in Amazon Inspector don’t precisely map to “danger accepted” or “false constructive” in Cisco Vulnerability Administration, so they’re handled as open vulnerabilities.
Able to get began?
Attain out to your Cisco consultant immediately to study extra about ingesting information from Amazon Inspector into Cisco Vulnerability Administration for a consolidated view of danger and efficient prioritization.
We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Related with Cisco Safety on social!
Cisco Safety Social Channels
Share:
