The Federal Bureau of Investigation and Cybersecurity & Infrastructure Safety Company warned in a joint advisory a couple of menace actor deploying a botnet that makes use of the Androxgh0st malware. This malware is able to amassing cloud credentials, reminiscent of these from AWS or Microsoft Azure and extra, abusing the Easy Mail Switch Protocol, and scanning for Amazon Easy Electronic mail Service parameters.
What’s the Androxgh0st malware?
The Androxgh0st malware was uncovered in December 2022 by Lacework, a cloud safety firm. The malware is written in Python and is primarily used to steal Laravel.env information, which comprise secrets and techniques reminiscent of credentials for high-profile purposes. For example, organizations can combine purposes and platforms reminiscent of AWS, Microsoft Workplace 365, SendGrid or Twilio to the Laravel framework, with all the purposes’ secrets and techniques being saved within the .env file.
The botnet hunts for web sites utilizing the Laravel internet software framework earlier than figuring out if the area’s root stage .env file is uncovered and comprises information for accessing extra companies. The info within the .env file could be usernames, passwords, tokens or different credentials.
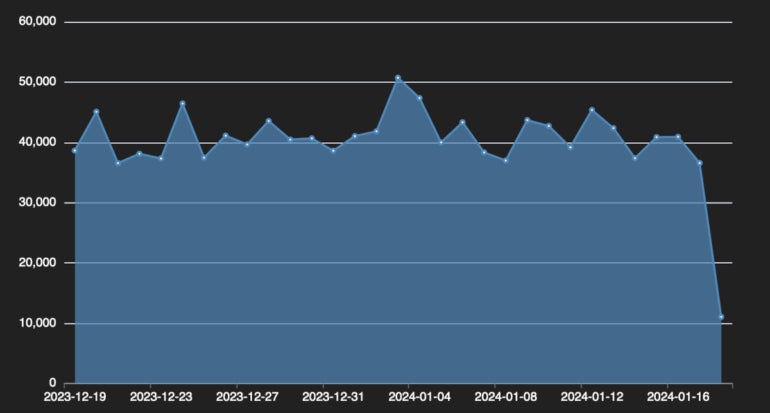
The cybersecurity firm Fortinet uncovered telemetry on Androxgh0st, which exhibits greater than 40,000 gadgets contaminated by the botnet (Determine A).
Determine A
The FBI/CISA advisory states: “Androxgh0st malware additionally helps quite a few features able to abusing the Easy Mail Switch Protocol (SMTP), reminiscent of scanning and exploiting uncovered credentials and software programming interfaces (APIs), and internet shell deployment.”
How can Androxgh0st malware exploit outdated vulnerabilities?
As well as, Androxgh0st can entry the Laravel software key; if that secret is uncovered and accessible, the attackers will attempt to use it to encrypt PHP code that’s handed to the web site as a price for the XSRF-TOKEN variable. That is an try to take advantage of the CVE-2018-15133 vulnerability in some variations of the Laravel internet software framework. A profitable try permits the attacker to remotely add information to the web site. CISA added the CVE-2018-15133 Laravel deserialization of untrusted information vulnerability to its Identified Exploited Vulnerabilities Catalog based mostly on this proof of lively exploitation.
The menace actor deploying Androxgh0st has additionally been noticed exploiting CVE-2017-9841, a vulnerability within the PHP Testing Framework PHPUnit that permits an attacker to execute distant code on the web site.
CVE-2021-41773 can be exploited by the menace actor. This vulnerability in Apache HTTP Server permits an attacker to execute distant code on the web site.
What is understood about Androxgh0st malware’s spamming objective?
Lacework wrote in late 2022 that “over the previous yr, almost a 3rd of compromised key incidents noticed by Lacework are believed to be for the needs of spamming or malicious electronic mail campaigns,” with the vast majority of the exercise being generated by Androxgh0st.
The malware has a number of options to allow SMTP abuse, together with scanning for Amazon’s Easy Electronic mail Service sending quotas, most likely for future spamming utilization.
The right way to defend from this Androxgh0st malware menace
The joint advisory from CISA and the FBI recommends taking the next actions:
- Hold all working techniques, software program and firmware updated. Specifically, Apache servers should be updated. As will be learn on this article, attackers are nonetheless in a position to set off an Apache Net server vulnerability that was patched in 2021.
- Confirm that the default configuration for all URIs is to disclaim entry until there’s a particular want for it to be accessible from the web.
- Guarantee Laravel purposes will not be configured to run in debug or testing mode as a result of it’d permit attackers to take advantage of weaknesses extra simply.
- Take away all cloud credentials from .env information and revoke them. As said by CISA and the FBI, “all cloud suppliers have safer methods to offer short-term, incessantly rotated credentials to code operating inside an internet server with out storing them in any file.”
- Overview any platforms or companies that use .env information for unauthorized entry or use.
- Seek for unknown or unrecognized PHP information, particularly within the root folder of the online server and within the /vendor/phpunit/phpunit/src/Util/PHP folder if PHPUnit is being utilized by the online server.
- Overview outgoing GET requests to file internet hosting platforms (e.g., GitHub and Pastebin), significantly when the request accesses a .php file.
As well as, it’s suggested to examine for any newly created person for any of the affected companies, as a result of Androxgh0st has been noticed creating new AWS cases used for extra scanning actions.
Safety options should be deployed on all endpoints and servers from the group to detect any suspicious exercise. When attainable, your IT division ought to deploy multifactor authentication on all companies the place attainable to keep away from being compromised by an attacker in possession of legitimate credentials.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.
