Cisco is a longtime companion of the Black Hat NOC and 2023 was our seventh 12 months supporting Black Hat Europe. Cisco is the Official Cellular Machine Administration, Malware Evaluation and DNS (Area Identify Service) Supplier.
We work with the opposite official suppliers to deliver the {hardware}, software program and engineers to construct and safe the community, for our joint buyer: Black Hat.
- Arista: Wired and Wi-fi Community Gear
- Corelight: Community Analytics and Detection
- NetWitness: Menace Detection & Response, Identification
- Palo Alto Networks: Community Safety Platform

The first mission within the NOC is community resilience. The companions additionally present built-in safety, visibility and automation, a SOC contained in the NOC.

Outdoors the NOC have been companion dashboards for the attendees to view the amount and safety of the community site visitors.
From Malware to Community Visibility
Cisco was first requested to offer automated malware evaluation, again in 2016. Our contributions to the community and safety operations developed, with the wants of the client.
The NOC leaders allowed Cisco (and the opposite NOC companions) to usher in further software program to make our inner work extra environment friendly and have better visibility; nevertheless, Cisco isn’t the official supplier for Prolonged Detection and Response, Community Detection and Response or collaboration.
- Cisco XDR: Menace Looking / Menace Intelligence Enrichment / Govt dashboards / Automation with Webex
- Cisco XDR Analytics (Previously Safe Cloud Analytics / Stealthwatch Cloud): community site visitors visibility and menace detection
- Cisco Webex: Incident notification and crew collaboration
The Cisco XDR Command Heart dashboard tiles made it simple to see the standing of every of the linked Cisco Safe applied sciences, and the standing of ThousandEyes brokers.

When the companions deploy to every convention, we arrange a world class community and safety operations middle in a couple of days. Our purpose stays community up time and creating higher built-in visibility and automation. Black Hat has the choose of the safety business instruments and no firm can sponsor/purchase their method into the NOC. It’s invitation solely, with the intention of range in companions, and an expectation of full collaboration. As a NOC crew comprised of many applied sciences and firms, we’re constantly innovating and integrating, to offer an general SOC cybersecurity structure resolution.
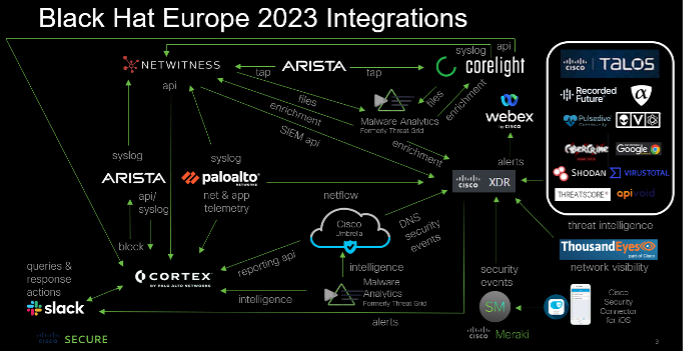
Beneath are the Cisco XDR integrations for Black Hat Europe, empowering analysts to research Indicators of Compromise (IOC) in a short time, with one search.
We respect alphaMountain.ai, Pulsedive and Recorded Future donating full licenses to Cisco, to be used within the Black Hat Europe 2023 NOC.

A core built-in expertise within the Black Hat NOC for Cisco is NetWitness sending suspicious recordsdata to Menace Grid (now Safe Malware Analytics). We expanded this in Black Hat Asia 2023 with Corelight additionally submitting samples. Over 4,600 samples have been submitted.

The NOC analysts additionally used Malware Analytics to research suspicious domains, with out the chance of an infection. An instance was an alert for cryptomining on the community by Umbrella, accessed by a pupil in a Black Hat coaching course.
Somewhat than going to the web site on a company or Black Hat belongings, we have been capable of work together with the web site within the glovebox, together with downloading and putting in the web site payload.
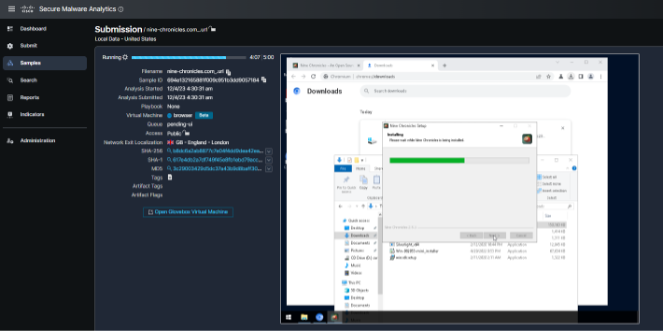
We allowed the payload to make the modifications on the digital machine, because the person skilled.

For cryptomining, we permit the exercise to happen, however alert the person that their system is getting used for that goal.
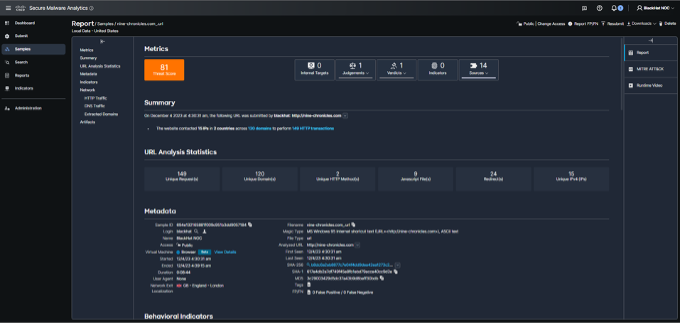
Because the payload was not malicious, we didn’t notify the person of an an infection.

XDR Analytics, by Abhishek Sha
XDR Analytics (previously Safe Cloud Analytics, or Stealthwatch Cloud) lets you achieve the visibility and steady menace detection wanted to safe your public cloud, non-public community and hybrid surroundings. XDR Analytics can detect early indicators of compromise within the cloud or on-premises, together with insider menace exercise and malware, coverage violations, misconfigured cloud belongings, and person misuse. These NDR (Community Detection and Response) capabilities are native performance inside Cisco XDR. Cisco XDR was out there beginning July 31st 2023, so we had some expertise underneath our belt for using its capabilities.
XDR Analytics outfitted us with the aptitude to establish a spread of alerts, considerably enhancing our cybersecurity measures at Black Hat.
Deciphering Cyber Threats: A Black Hat Case Research in XDR Analytics
Whereas scanning web hosts is a typical apply in cybersecurity, it’s vital to notice that the context and goal of those scans can considerably influence the seriousness of the scenario. If these scans have been to shift focus in the direction of different convention contributors or, extra critically, in the direction of the community infrastructure itself, it might immediate a extra critical response.
This situation underscores the necessity for steady vigilance and a proactive method in monitoring and responding to potential cyber threats. That is the essence of efficient cybersecurity administration – a course of that’s continuously examined, improved, and fortified within the face of potential threats.
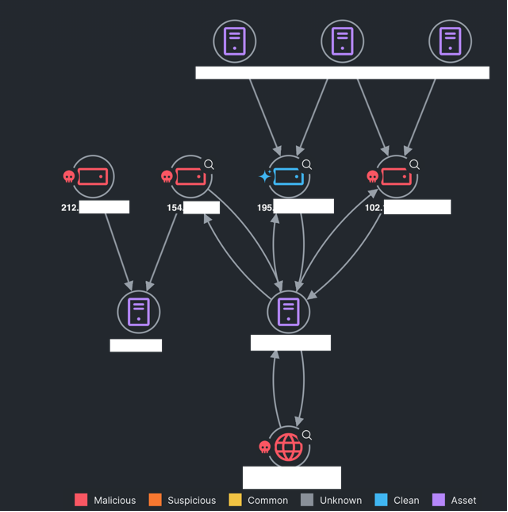
Throughout our community vigilance at Black Hat, Ivan and I encountered a situation that clearly highlighted the essential position of XDR Analytics. XDR Analytics raised an alert when it detected that a number of inner IP addresses have been speaking with sure exterior IP addresses. Intriguingly, these exterior IP addresses have been on our blocklist for manufacturing safety environments.

Leveraging the netflow telemetry we have been receiving, we employed the Occasion Viewer characteristic on XDR Analytics to discern the kind of site visitors being transmitted to these addresses. On all noticed logs, the one protocol was ICMP.
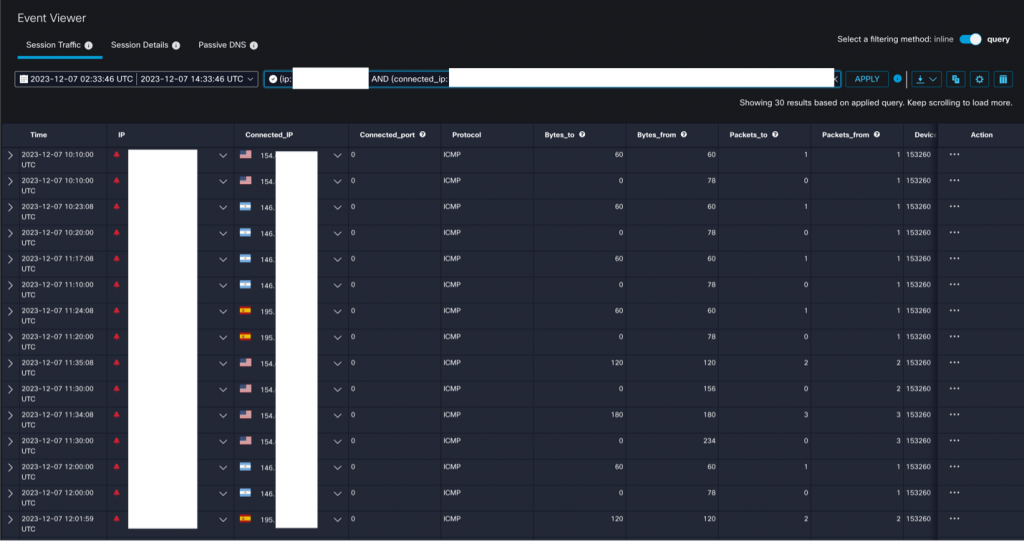
A full search confirmed that no site visitors other than ICMP linked to the exterior IPs.
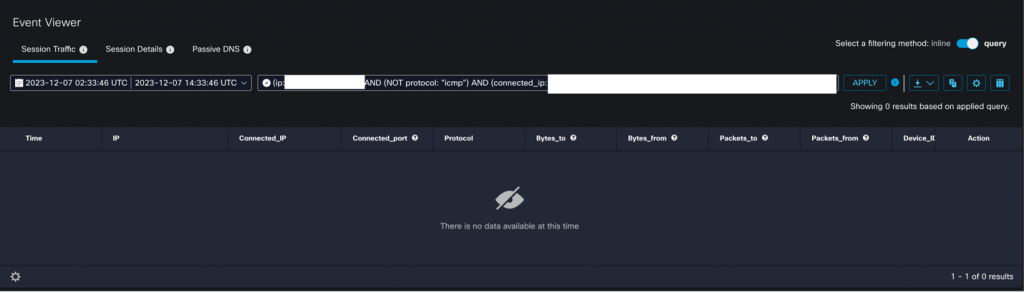
By using graphs in XDR Analytics, we gained insights into the amount of site visitors despatched to the exterior IP addresses. This proved instrumental in figuring out whether or not any potential ICMP tunneling was going down, primarily based on the dimensions of the general site visitors.

We then targeted our investigative efforts on these suspicious exterior IP addresses utilizing Cisco XDR. The examination revealed that this IP was flagged on different blocklists as properly.

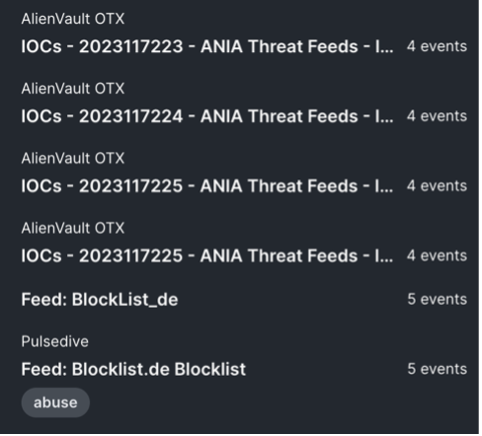
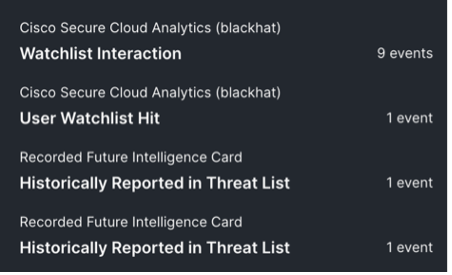
Additional evaluation on the Cisco XDR graph disclosed a community of different endpoints that had additionally been interacting with these doubtful IP addresses. This revelation uncovered the far-reaching affect of those IPs and enabled us to visualise the assorted interconnected actions.
Lastly, we resolved the IP addresses on Umbrella and deduced that these IP addresses have been related to a “Non-public Web Entry VPN”. It appeared that the endpoint was testing the reachability of all these relays hosted in several places.
Regardless of this site visitors being innocuous, we capitalized on XDR and XDR Analytics to realize a greater understanding and context of this incident. This expertise underscores the efficacy of those instruments in enhancing cybersecurity defenses.
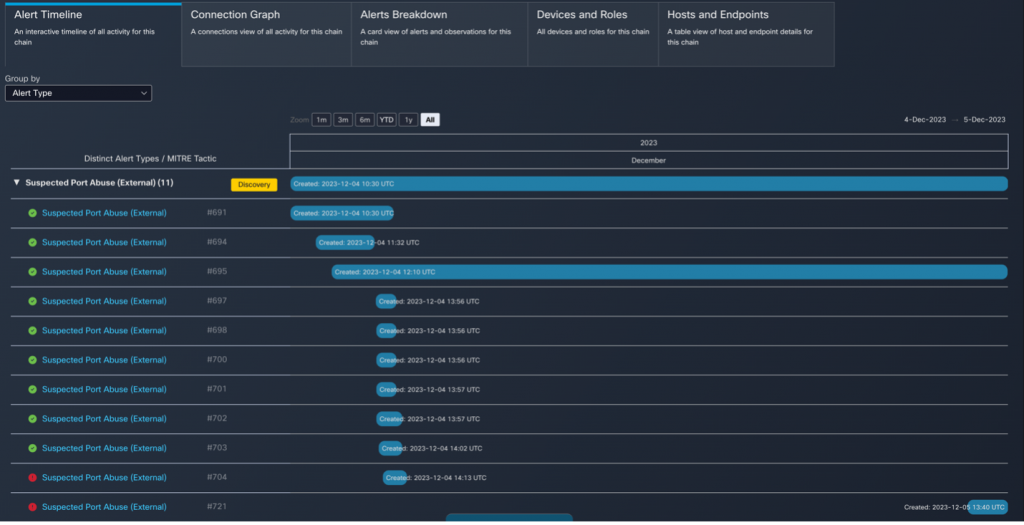
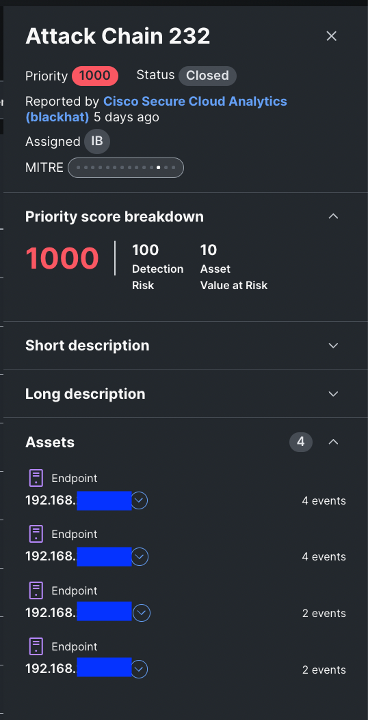
Mastering Menace Detection with Assault Chains
XDR Assault Chain is a characteristic that enables us to correlate a number of alerts into a bigger investigation. We use extracted alert meta information to find out what the alerts have in widespread, which we consult with as widespread indicators. Widespread indicators embody units, IP addresses, host names, and usernames. We then observe the MITRE ATT&CK® framework to additional establish the techniques, methods, and procedures (TTPs) to mannequin the sequencing of actions and menace behaviors which may very well be early indications of an assault.
On this occasion, we’re observing an assault chain comprising a number of “Suspected Port Abuse (Exterior)” occasions. Sometimes, with out an assault chain, every of those occasions would should be investigated individually, a course of that may very well be time-consuming and probably much less efficient.

Nevertheless, the fantastic thing about an assault chain lies in its skill to consolidate a number of alerts right into a singular, interconnected occasion. This methodology supplies a holistic overview of the assorted alerts, the units concerned, and their respective roles, all inside the framework of a single mixed occasion.
The ability of this method is that it eliminates the necessity for an exhaustive investigation of every separate alert. As a substitute, it presents a complete, contextualized view of the scenario, enabling a extra environment friendly and efficient response to potential threats.
With this data, we have been capable of work with the menace hunters of NetWitness, Palo Alto Networks and Corelight, to find out the chance to the community and attendees. Actions involving malware what can be blocked on a company community should be allowed, inside the confines of Black Hat Code of Conduct.
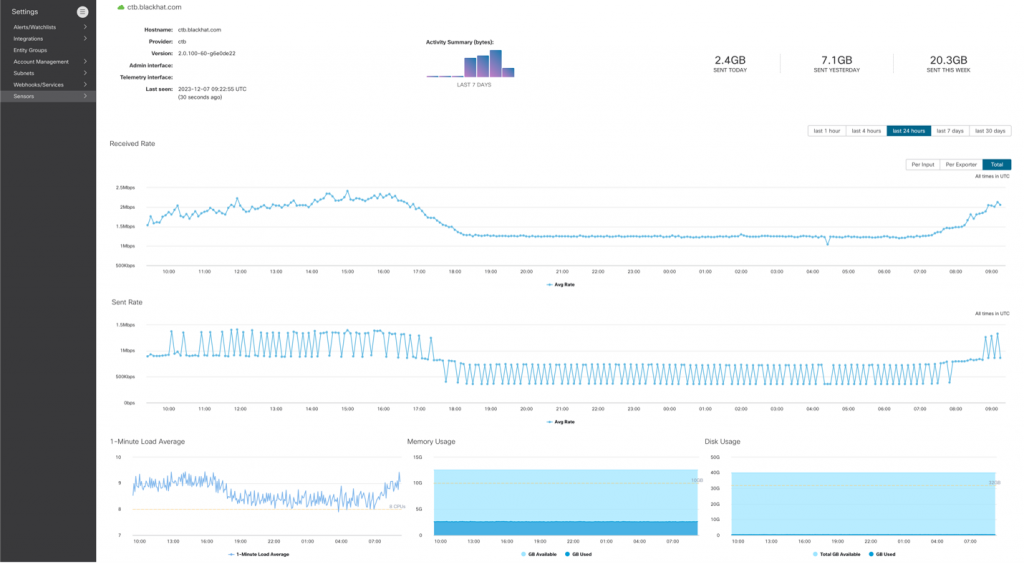
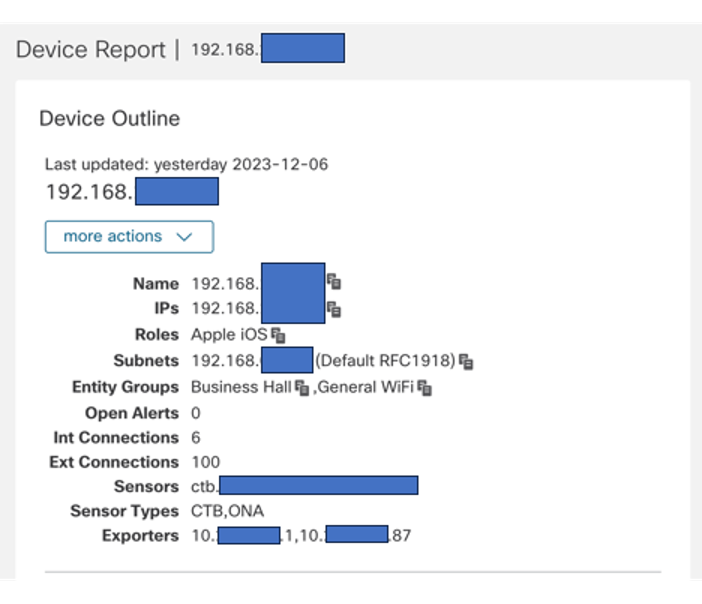
Black Hat Insights: Cisco Telemetry Dealer
Cisco Telemetry Dealer (CTB) acts as a foundational pillar for the clever telemetry airplane, thereby future-proofing the telemetry structure. It enhances visibility and context into the telemetry that drives the merchandise that depend on it, facilitating telemetry brokering, filtering, and sharing. The Telemetry Dealer is the end result of years of administration, troubleshooting, remodeling, and sharing telemetry to empower Safety and Community Analytics merchandise.
On the Black Hat occasion, we employed the Telemetry Dealer to course of a SPAN (Switched Port Analyzer is a devoted port on a swap that takes a mirrored copy of community site visitors from inside the swap to be despatched to a vacation spot) of all community site visitors, together with the Netflow generated from Palo Alto Networks firewalls. This was a part of our NOC collaboration and integrations. We then made all this information out there to the menace hunters in Cisco XDR.
A typical Telemetry Dealer deployment necessitates each a dealer node and a supervisor node. To attenuate our on-premises footprint, we selected to handle the dealer node by XDR Analytics. This performance was activated by the XDR Analytics Engineering crew on our Black Hat XDR Analytics portal from the backend, as it’s at present in beta. This enabled us to handle the dealer node and assessment the metrics immediately from the cloud.
We additionally put in an extra plugin often known as the Circulation Generator Plugin. This plugin enabled us to generate Netflow telemetry from the ingested SPAN site visitors. With the beta code, we have been lucky to have the assist of the engineering crew to check the most recent and most superior expertise Cisco has to supply. A particular shoutout to the engineering crew for his or her invaluable assist.
Unleashing the Energy of Cisco XDR Automate at Black Hat Europe
With the ever-evolving technological panorama, automation stands as a cornerstone in attaining XDR outcomes. It’s certainly a testomony to the prowess of Cisco XDR that it boasts a totally built-in, strong automation engine.
Cisco XDR Automation embodies a user-friendly, no-to-low code platform with a drag-and-drop workflow editor. This progressive characteristic empowers your Safety Operations Heart (SOC) to hurry up its investigative and response capabilities. You may faucet into this potential by importing workflows straight from Cisco or by flexing your artistic muscular tissues and crafting your individual.
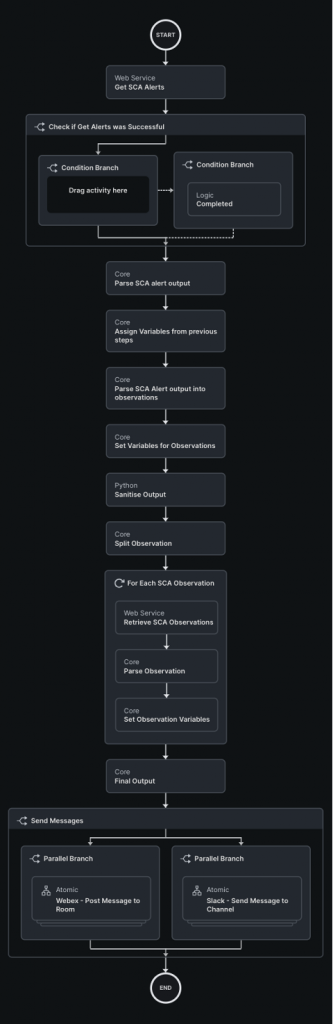
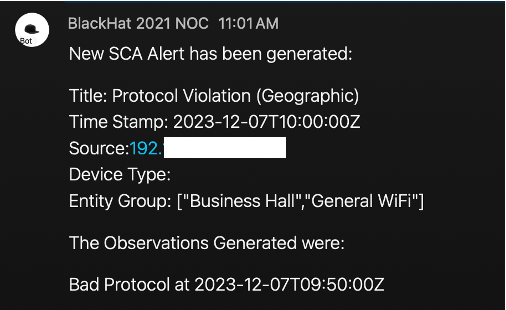
Cisco XDR introduces a trailblazing idea often known as Automation Guidelines. This recent tackle automation guarantees to revolutionize the way in which you work together with the system. Through the Black Hat Europe occasion, we flexed our ingenious muscular tissues and dropped at life an XDR Automate workflow. This workflow was designed to spring into motion each time XDR Analytics posted an incident. The workflow would delve into the center of the alert, extracting essential particulars such because the alert description, publish time, entity teams, and observations. The parsed outcomes have been then broadcasted on Webex Groups through a message and concurrently posted on Slack. This ensured that different menace hunters might readily eat the knowledge. Moreover, the workflow might be shared on GitHub, encouraging a wider viewers to grasp and respect the automation course of.
The automation output is beneath. Within the realm of cybersecurity, Cisco XDR Automate is pushing the boundaries, redefining how we understand automation and its limitless potentialities.
“Collaboration” and “Continuity” – for profitable menace looking, by Ivan Berlinson
Throughout Black Hat, the NOC opens early earlier than the occasion and closes later after the trainings/briefings full for the day. Because of this each analyst place should be lined by a bodily, uninterrupted presence for about 11 hours per day. Even with the utmost dedication to your position, typically you want a break, and a brand new potential incident doesn’t wait till you’ve completed the earlier one.

Abhishek and I shared the position of Cisco XDR analyst, with morning and afternoon shifts. Now we have labored intently collectively to deal with incidents or alerts from Cisco XDR analytics and to actively hunt threats. It was an incredible collaboration! It was vital that we didn’t work in silos and that we acted as a crew to verify we maximized all our efforts. To do that, we after all wanted good communication, however we additionally wanted a platform that will assist us and allow us to doc and share data rapidly and simply (the incident we’re at present engaged on, what we’ve discovered, what we’ve completed…).
The Cisco XDR incident supervisor and ribbons (with its browser extension) have been an incredible assist and saved us quite a lot of time. Let’s rapidly see how we used them in a typical investigation.
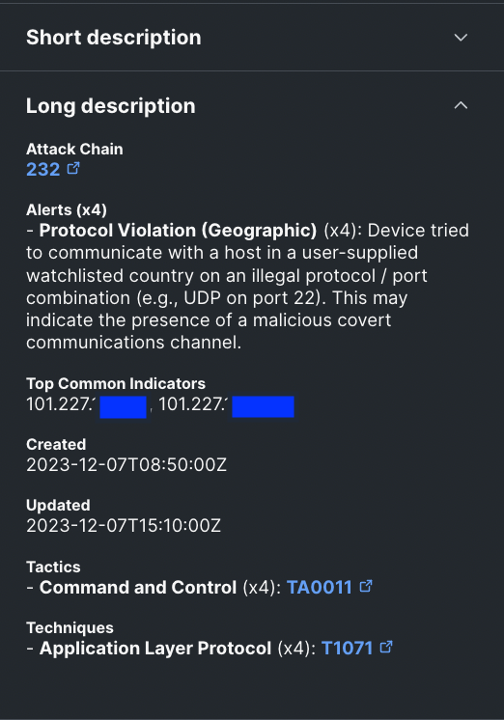
Whereas I used to be performing a menace hunt primarily based on a Malware Analytics (Menace Grid) report displaying phishing indicators, XDR analytics alerted us about a number of communications to locations on an inventory of nations to be monitored and utilizing a non-standard protocol/port mixture.
Cisco XDR – Incident abstract
I took a fast take a look at the incident, and due to XDR assault chain and computerized enrichment, I had an prompt view of the belongings impacted and the a number of locations concerned.

Cisco XDR – Incident principal view (with auto-enrichment)
Telemetry from the NetWitness integration enriched the incident and confirmed the site visitors, however the built-in menace intelligence sources didn’t present any malicious verdicts or menace indicators associated to those IP addresses. Additional investigation was required to substantiate this potential incident.
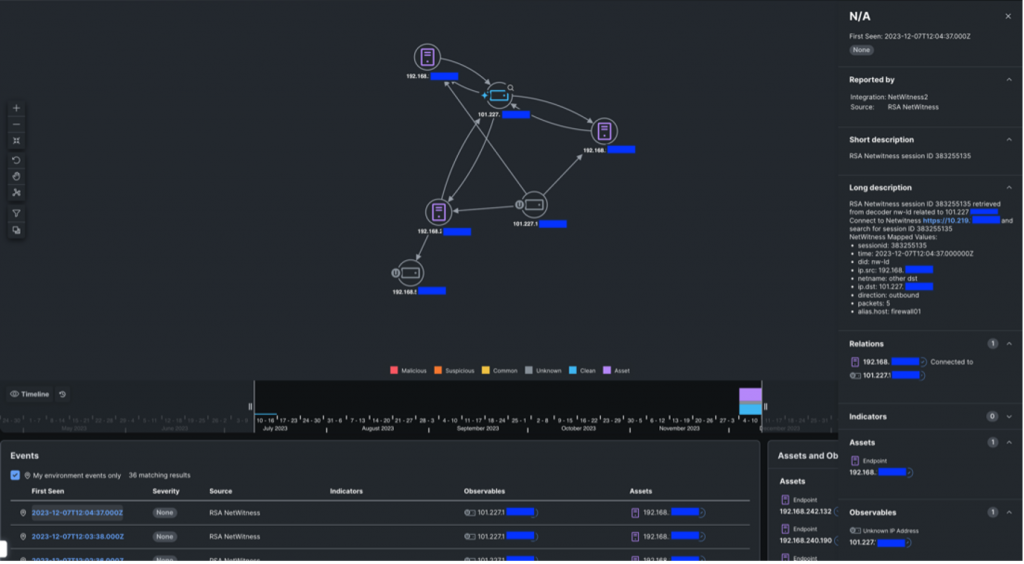
Investigation with telemetry from NetWitness
I added a be aware to the incident as a part of the “Verify Incident” step of the response plan, however as I used to be already on one other exercise, I requested Abhishek to get into the sport.
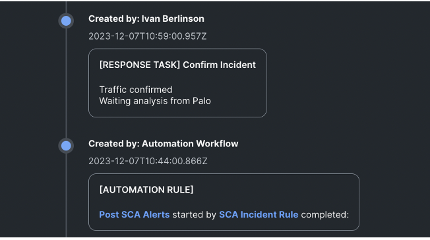
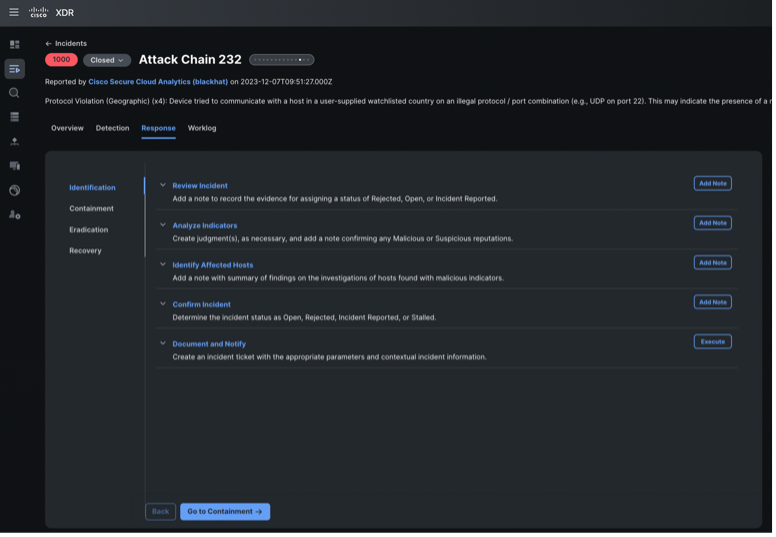
Cisco XDR – Guided Response
Abhishek was capable of additional examine communication to these IPs within the uncooked community flows collected by XDR analytics and collaborate with the NetWitness crew, who can look deep inside packet. However he doesn’t want to jot down down the IPs on paper or memorize them, we will use the Cisco XDR ribbon built-in in our browser to in one-click extract any observables in an internet web page.

Add observables to casebook utilizing Cisco XDR ribbon (browser-plugin)
We are able to then add them to a casebook shared robotically between us and out there in all places.

Casebook out there for Abhishek within the XDR Analytics console
A couple of minutes later, I had completed with my earlier file and was assured about going to lunch, figuring out that Abhishek was on the case and had all the knowledge he wanted.
With the assistance of the Palo Alto analyst, it was confirmed that the site visitors was reputable (QUIC – HTTP/3).

Affirmation from Palo Alto
Listed here are the browser extensions on your personal SOC use:
Community Visibility with ThousandEyes, by Adam Kilgore and Alicia Garcia Sastre
Black Hat Europe 2023 is the third consecutive convention with a ThousandEyes (TE) presence, following a proof of idea in Black Hat Asia 2023 and an preliminary deployment at Black Hat USA 2023. Constructing upon our first full deployment in Vegas, we have been targeted on improving deployment course of, information baselining, and monitoring procedures.
{Hardware} and Deployment Course of

A few of the {hardware} we dropped at the convention
Identical to Black Hat USA 2023, we deployed 10 TE brokers on Raspberry Pi’s. Nevertheless, since ExCel London is a smaller venue, we had the identical variety of brokers to unfold throughout a smaller space—we nonetheless didn’t really feel like we had a full Thousand Eyes, however positively extra visibility. We unfold that visibility throughout core switching, Registration, the Enterprise Corridor, two- and four-day coaching rooms, and Keynote areas.
We additionally added a couple of equipment from classes discovered in Vegas. Deploying TE brokers on micro-SDs is a time-consuming course of which requires connecting the micro-SD to a laptop computer utilizing a USB adapter. We invested in two adapters that may join 4 USB adapters without delay for extra streamlined deployment and scaling.
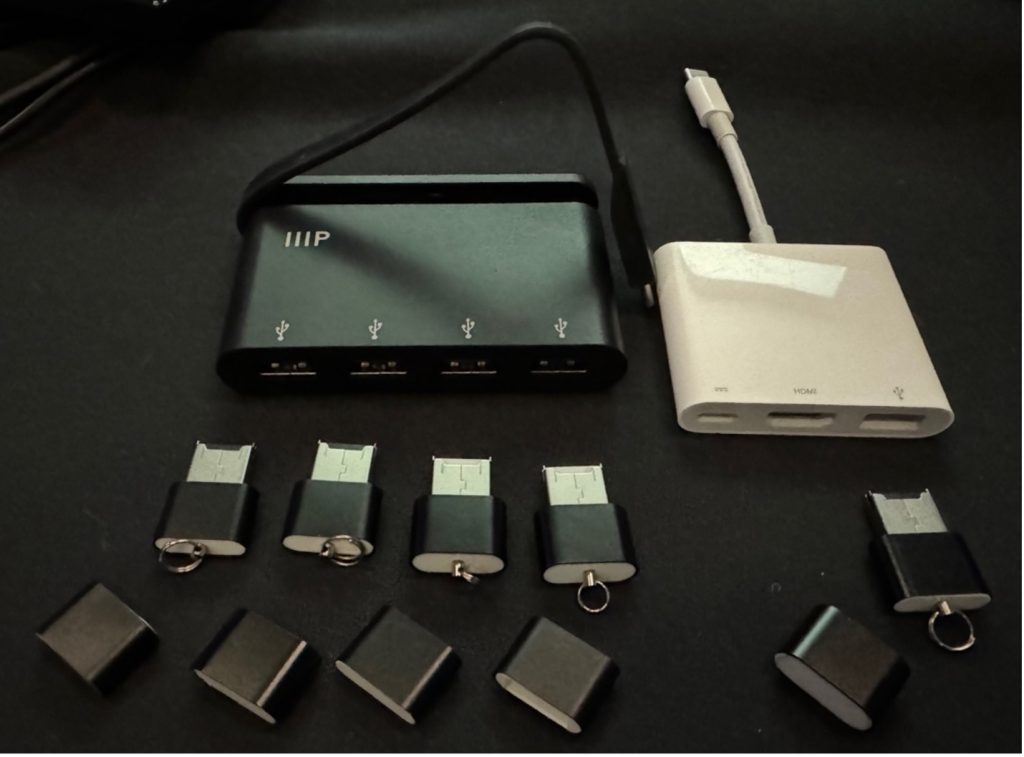
Economies of scale
At BH USA, we additionally developed a technique for deploying TE brokers wirelessly on Raspberry Pi (as lined on this weblog put up), regardless that this performance isn’t technically supported. At BH Europe, our intention was to depend on wired Pi brokers for the majority of the monitoring; nevertheless, the wi-fi entry factors shipped to the convention didn’t have a free ethernet port. Due to this we ended up doing a primarily wi-fi deployment once more, plus two wired brokers linked to switching infrastructure. The brand new wi-fi deployment revealed some documentation and course of enhancements to roll into the prior weblog put up.
Enabling wi-fi on the ThousandEyes Pi picture additionally makes the Pi extra vulnerable to overheating. The server room in London ExCel the place we did our preliminary provisioning had a cooling drawback and reached 28 levels Celsius (82 F) at one level. The warmth within the room precipitated a really quick failure of the wi-fi adapter, which initially made it seem that the wi-fi was not working in any respect. Nevertheless, we finally untangled the documentation and warmth associated issues and received all of the Pi’s deployed, the place they functioned stably all through the convention, with only some overheating incidents.
Adjustments in out there personnel and {hardware} additionally necessitated a change within the Linux platform for configuring the scripts for persistent wi-fi deployment. We went with Ubuntu through VMWare Fusion on Mac laptops, which offered a clean deployment sequence.
Monitoring, Alerting, and Baselining
The wi-fi community at BH Europe had much less latency variation than BH USA, which required tuning of alert thresholds to scale back noise. At BH USA, we deployed a rule that fired when the latency on any agent exceeded two commonplace deviations above baseline. Nevertheless, in BH Europe this alert was firing on latency modifications that have been statistically important, however very minor in actual world phrases. For instance, the alert beneath fired when latency elevated 5.4ms+ above a 7.3ms baseline.

To regulate for smaller variations, we added a minimal threshold of 30ms change above baseline. This resulted in a a lot smaller set of extra helpful alerts, whereas nonetheless sustaining visibility into altering latency circumstances earlier than latency reached noticeably degraded ranges.
Trains, Planes, and Wi-fi Entry Factors
On the final day of the convention, NOC morning employees discovered the wi-fi community was inaccessible half-hour earlier than the convention opened for the day. Nothing will get the blood pumping like a community failure proper earlier than enterprise hours. Nevertheless, an expedited investigation revealed that solely the NOC was affected, and never the broader convention wi-fi infrastructure.
Troubleshooting revealed that the SSID was out there, however many of the endpoints couldn’t detect it. A fast collaboration with our mates at Arista revealed that the endpoints making an attempt to hook up with 5 GHz have been having points, whereas the endpoints that have been linked at 6 GHz have been all high-quality—an vital element.
This was according to what we noticed within the ThousandEyes portal. There was one engineer with a ThousandEyes endpoint agent working earlier than the outage occurred. We jumped to agent views to examine Wi-Fi stats.
Whereas we have been investigating, the SSID got here again at 5 GHz.
Reviewing the TE endpoint logs, we discovered that the endpoint was linked to wi-fi channel 116 earlier than the outage.
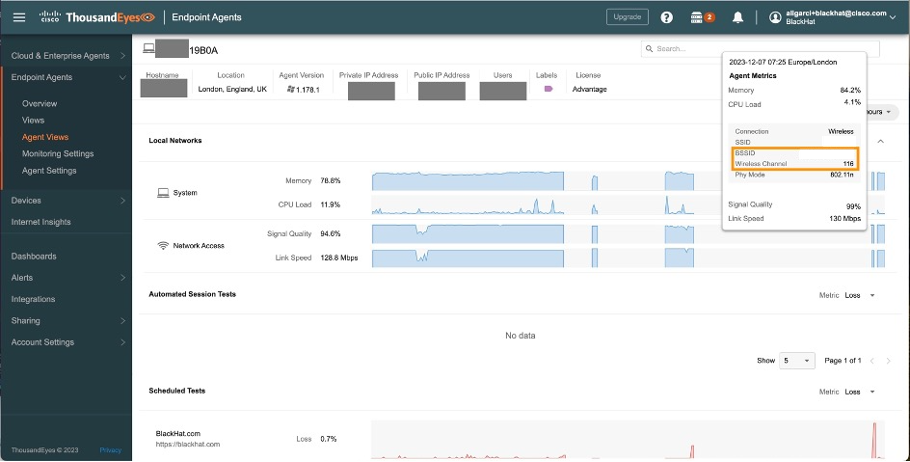
After restoration the endpoint was linked to channel 124.
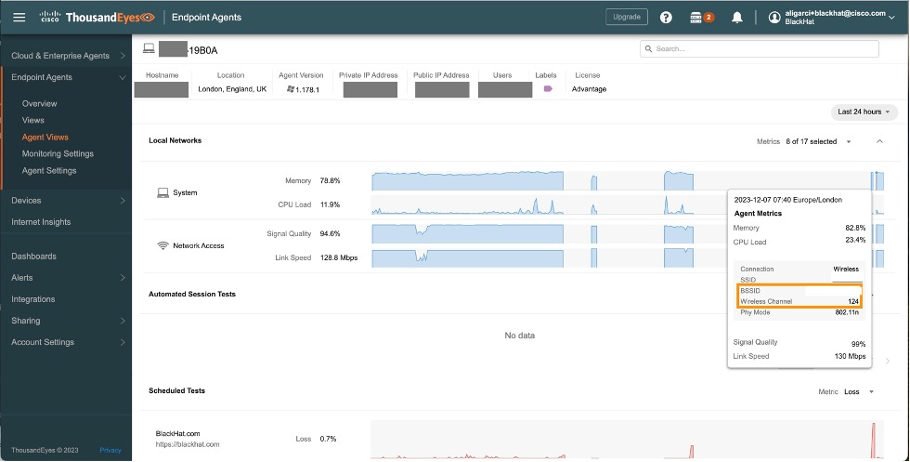
Through the outage the endpoint was not able to connecting to the Wi-Fi, creating a niche within the logs the place no channel or sign energy was out there. The channel change was indicative of the SSID coming again up and recalculating the perfect channel to promote the SSID.
So why did the wi-fi channel of the SSID change and what was the set off? Right here comes the fascinating half: The Black Hat convention is hosted at ExCeL London, lower than 4 km away from the London Metropolis airport. Keep in mind the preliminary channel of the SSID? It was 116, which is a Dynamic Frequency Choice (DFS) channel. These channels share the spectrum with climate radar and radar programs.
To share the usage of these channels in Wi-Fi, a mechanism was put in place by regulators to prioritise radar utilization, and that is precisely what DFS does. Wi-Fi units will hear for radar occasions and both cease utilizing the channels or robotically transfer off these channels after they detect radar occasions.
As we’re so near the airport, isn’t uncommon that one DFS occasion occurred. We’re simply fortunate it didn’t occur extra typically.

Do you wish to see the entire evaluation for your self? Because of a really useful characteristic of ThousandEyes, you’ll be able to. All the knowledge of this mini outage was captured in a net accessible report. Be happy to click on round and discover all of the related data for your self. The outage began at 7.31 am. Essentially the most insightful view could be discovered at Scheduled exams -> Community -> Click on on the dotted strains to show all of the nodes within the path visualization and see metrics extra clearly.
Meraki Programs Supervisor, by Paul Fidler and Connor Loughlin
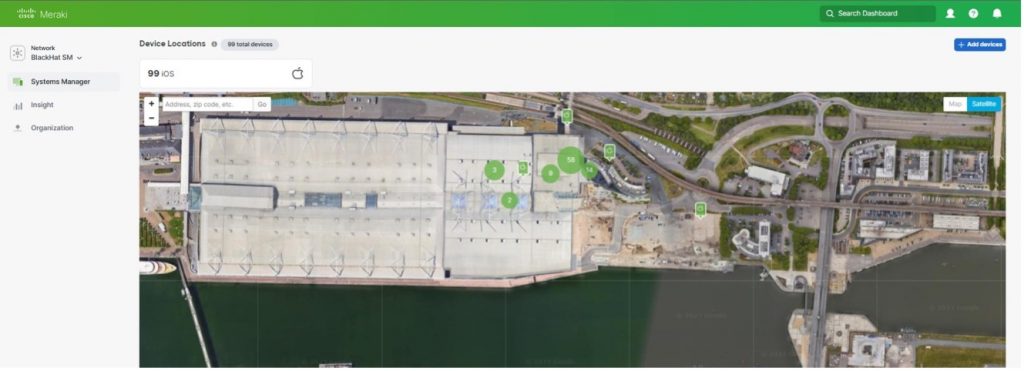
Our eighth deployment of Meraki Programs Supervisor because the official Cellular Units Administration platform went very easily, and we launched a brand new caching operation to replace iOS units on the native community, for pace and effectivity. Going into the occasion, we deliberate for the next variety of units and functions:
- iPhone Lead Scanning Units: 68
- iPads for Registration: 9
- iPads for Session Scanning: 12
- Variety of units deliberate in complete: 89
We registered the units prematurely of the convention. Upon arrival, we turned every system on.

Then we ensured Location Companies enabled, at all times on.

As a substitute of utilizing a mass deployment expertise, like Apple’s Automated Machine Enrollment, the iOS units are “ready” utilizing Apple Configurator. This contains importing a Wi-Fi profile to the units as a part of that course of. In Las Vegas, this Wi-Fi profile wasn’t set to auto be a part of the Wi-Fi, leading to the necessity to manually change this on 1,000 units. Moreover, 200 units weren’t reset or ready, so we had these to reimage as properly.
Black Hat Europe 2023 was totally different. We took the teachings from US and coordinated with the contractor to arrange the units. Now, should you’ve ever used Apple Configurator, there’s a number of steps wanted to arrange a tool. Nevertheless, all of those could be actions could be mixed right into a Blueprint.
For Black Hat Europe, this included:
- Wi-Fi profile
- Enrollment, together with supervision
- Whether or not to permit USB pairing
- Setup Assistant pane skipping
In Meraki Programs Supervisor, we managed the purposes by the assigned use, designated by Tags. After we got here in on the primary morning of the Briefings, three iPhones wanted to be modified from lead scanning within the Enterprise Corridor, to Session Scanning for the Keynote, so the attendees might fill the corridor sooner. Reconfiguring was so simple as updating the Tags on every system. Moments later, they have been prepared for the brand new mission…which was vital because the Keynote room crammed to capability and needed to go to an overflow room.

We additionally have been capable of verify the bodily location of every system, if wiping was required because of loss or theft.
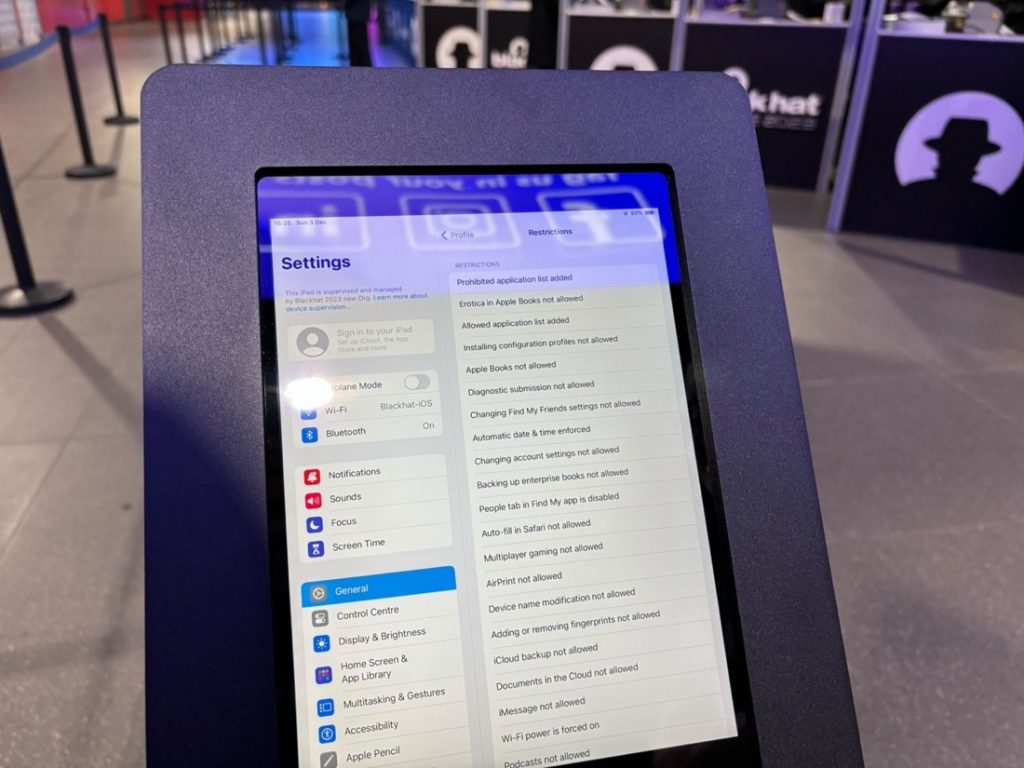
Beneath you’ll be able to see web page considered one of 4 pages of Restrictions imposed by Meraki Programs Supervisor.
When it was time for the attendees to register, they simply displayed their QR code from their private cellphone, as acquired in e-mail from Black Hat. Their badge was immediately printed, with all private particulars secured.

This goes with out saying, however the iOS units (Registration, Lead Seize and Session Scanning) do have entry to non-public data. To make sure the safety of the info, units are wiped on the finish of the convention, which could be accomplished remotely by Meraki Programs Supervisor.
Content material Caching
One of many greatest issues affecting the iOS units in BH USA 2023 was the quick must each replace the iOS system’s OS because of a patch to repair a zero-day vulnerability and to replace the Black Hat iOS app on the units. There have been a whole bunch of units, so this was a problem for every to obtain and set up. So, I took the initiative into wanting into Apple’s Content material Caching service constructed into macOS.
Now, simply to be clear, this wasn’t caching EVERYTHING… Simply Apple App retailer updates and OS updates.
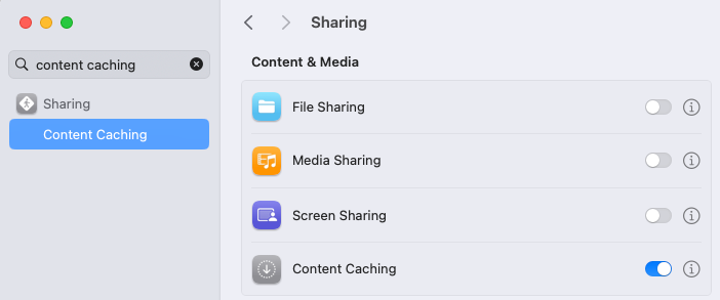
That is turned on withing System Setting and begins working instantly.
I’m not going to get into the weeds of setting this up, as a result of there’s a lot to plan for. However, I’d counsel that you simply begin right here. The setting I did change was:
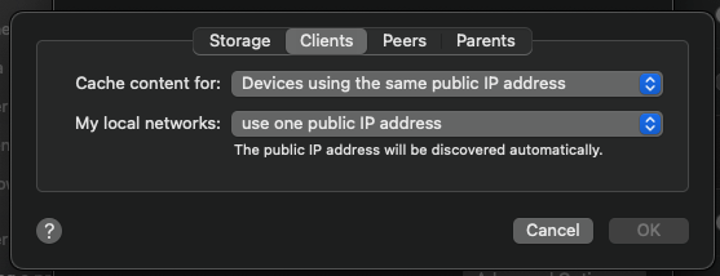
I checked to see that we had one level of egress from Black Hat to the Web. Apple doesn’t go into an excessive amount of element as to how this all works, however I’m assuming that the caching server registers with Apple and when units examine in for App retailer / OS replace queries, they’re then instructed the place to look on the community for the caching server.
Instantly after turning this on, you’ll be able to see the default settings and metrics:
% AssetCacheManagerUtil settings
Content material caching settings:
AllowPersonalCaching: true
AllowSharedCaching: true
AllowTetheredCaching: true
CacheLimit: 150 GB
DataPath: /Library/Software Assist/Apple/AssetCache/Information
ListenRangesOnly: false
LocalSubnetsOnly: true
ParentSelectionPolicy: round-robin
PeerLocalSubnetsOnly: true
And after having this run for a while:
% AssetCacheManagerUtil settings
Content material caching standing:
Activated: true
Energetic: true
ActualCacheUsed: 528.2 MB
CacheDetails: (1)
Different: 528.2 MB
CacheFree: 149.47 GB
CacheLimit: 150 GB
CacheStatus: OK
CacheUsed: 528.2 MB
MaxCachePressureLast1Hour: 0%
Mother and father: (none)
Friends: (none)
PersonalCacheFree: 150 GB
PersonalCacheLimit: 150 GB
PersonalCacheUsed: Zero KB
Port: 49180
PrivateAddresses: (1)
x.x.x.x
PublicAddress: 86.28.74.239
RegistrationStatus: 1
RestrictedMedia: false
ServerGUID: xxxxxxxxxxxxxxxxxx
StartupStatus: OK
TetheratorStatus: 1
TotalBytesAreSince: 2023-12-01 13:35:10
TotalBytesDropped: Zero KB
TotalBytesImported: Zero KB
TotalBytesReturnedToClients: 528.2 MB
TotalBytesStoredFromOrigin: 528.2 MB
Now, helpfully, Apple additionally pop this information periodically right into a database situated at:
Library/Software Assist/Apple/AssetCache/Metrics/Metrics.db in a desk referred to as ZMETRICS
Visualising this information: Studying from macOS Metrics.db
Impressed by a weblog I learn (impressed as a result of I couldn’t get the ruby script to work) I set off to attempt to create a entrance finish to this utilizing Grafana. After putting in a SQLIte plug in into Grafana, I might finally see information in Grafana, which was nice, however the Unix date appeared VERY from 1993. I spent two hours making an attempt to wrangle the info into one thing usable and viewable on a graph to no finish, so I gave up.
Nevertheless, it’s wonderful the distinction a day makes. I went again to Grafana and the SQLite db, and had some success:
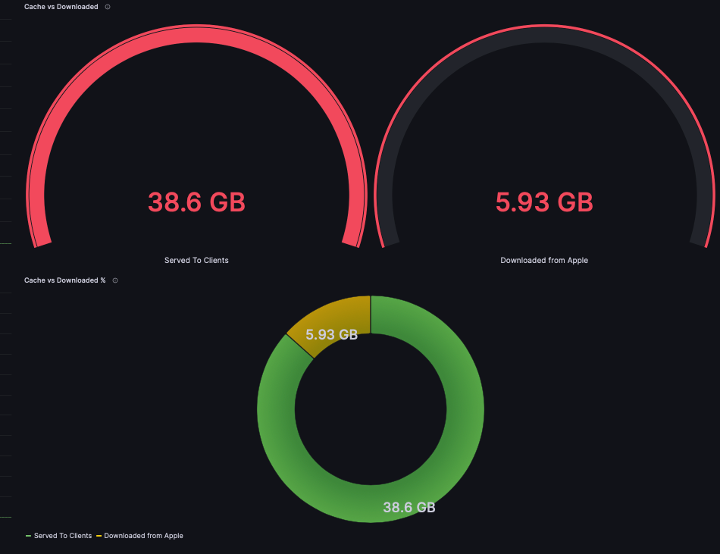
This diagram exhibits the cache vs utilization of cache. Keep in mind that there was a single OS replace, and solely a handful of purposes on the managed iOS units (in addition to updates for the Mac Mini that caching server is working on).
I additionally perservered with a historical past of cache utilization:
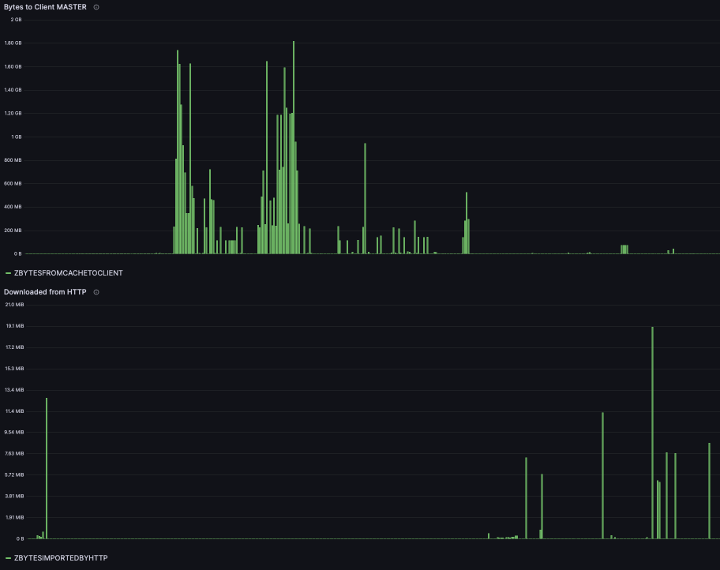
Attempt as I would, I couldn’t discover a solution to present the dates throughout the X Axis. I’ll persevere with this for Black Hat Asia 2024.
Visualising this information: Studying from my very own database
Firstly, I reused a few of the easy code to govern the info from the AssetCacheManagerUtil settings command. I then created a script that first created a SQLite database, after which, each 900 seconds, put the info into it. The code to do that is right here on GitHub.
After working with the info in right here, it appears incomplete. I’ll endeavor to work on this in order that the info is extra plausible for Singapore. In principal, nevertheless, this seems like a greater solution to retailer the info. Cache Strain, for instance, doesn’t seem within the database.
Area Identify Service Statistics and Streamlining NOC Menace Looking by Alex Calaoagan
Since 2017, we’ve got been monitoring DNS stats on the Black Hat conferences, and 12 months over 12 months (besides over the course of the pandemic), the present has continued to develop. That progress is mirrored within the DNS site visitors that we seize.
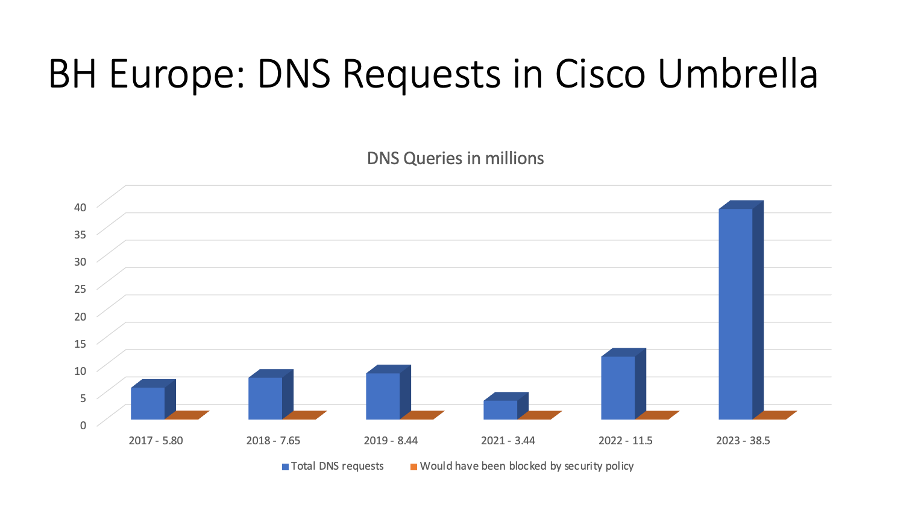
With over 38M DNS requests made, BH Europe 2023 has been, by far, the biggest London present on report. The large bounce in DNS requests could be attributed not simply to progress, but in addition to the visibility developments we made at BH Asia 2023, earlier this 12 months in Singapore.
*Fast reminder from Singapore: Working with Palo Alto Networks, we compelled attendees, through a firewall redirect initiated by Palo Alto Networks, to make use of our resolvers. With out this transformation, Umbrella wouldn’t see the site visitors in any respect, as these machines with hardcoded DNS, whether or not it was 1.1.1.1 (Cloudflare) or 8.8.8.8 (Google), have been capable of bypass our Digital Home equipment.
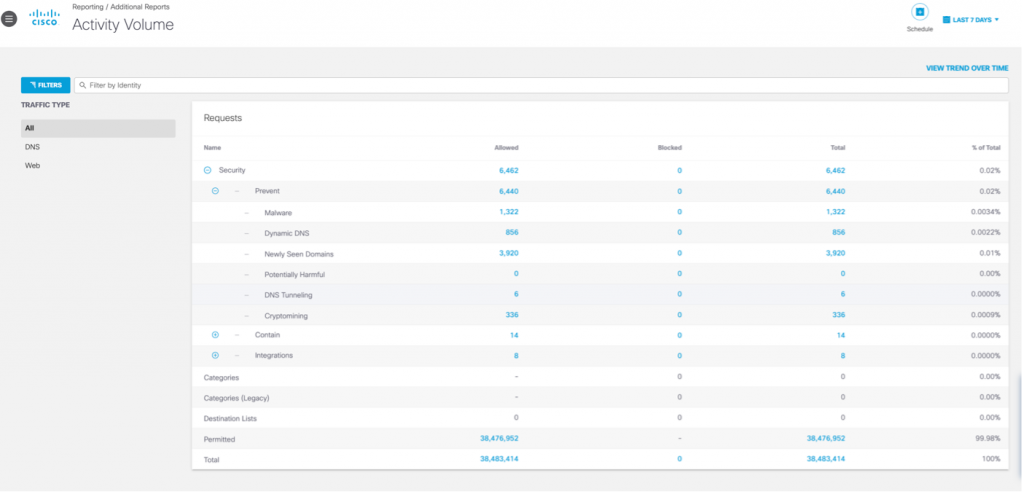
The Exercise quantity view from Umbrella offers a top-level stage look of actions by class, which we will drill into for deeper menace looking. On development with the earlier BH Europe occasions, the highest Safety classes have been Malware and Newly Seen Domains.
In a real-world surroundings, of the 38M requests that Umbrella noticed, over 6,000 of them would have been blocked by our default safety insurance policies. Nevertheless, since this can be a place for studying, we usually let every thing fly (extra on that later).

App Discovery in Umbrella offers us a fast snapshot of the cloud apps in use on the present. In step with Black Hat’s progress through the years, the variety of cloud apps in play has steadily risen. This quantity tends to observe attendance ranges, so no shock right here.
2021: 2,162 apps
2022: 4,159 apps
2023: 4,340 apps
 Taken with what apps attendees hit probably the most? Right here you go. The one surprises have been Slack (WhatsApp being the incumbent…we’re in Europe, proper?) and 9 Chronicles (who knew Block Chain MMORPG gaming was a factor? I actually didn’t).
Taken with what apps attendees hit probably the most? Right here you go. The one surprises have been Slack (WhatsApp being the incumbent…we’re in Europe, proper?) and 9 Chronicles (who knew Block Chain MMORPG gaming was a factor? I actually didn’t).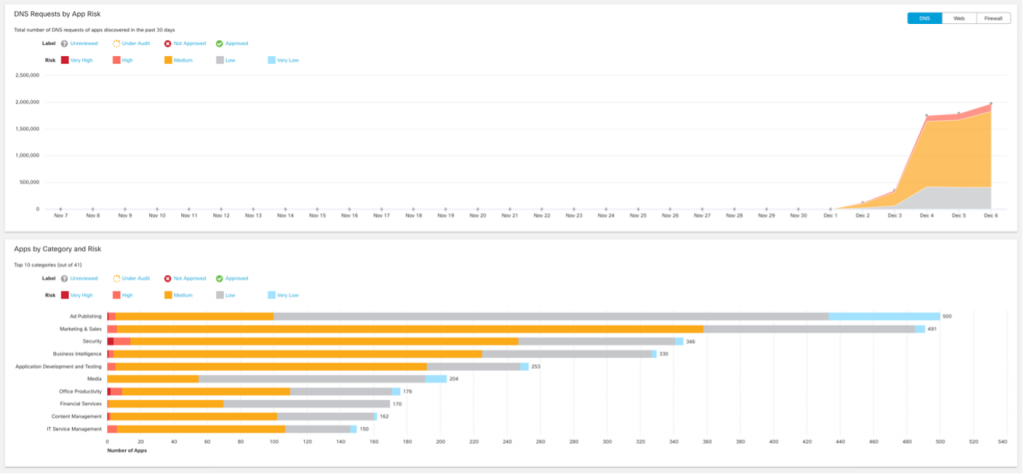
Umbrella additionally identifies dangerous cloud purposes. Ought to the necessity come up, we will block any software through DNS, comparable to Generative AI apps, Wi-Fi Analyzers, or anything that has suspicious undertones. Once more, this isn’t one thing we’d usually do on our Basic Wi-Fi community, however there are exceptions. For instance, now and again, an attendee will be taught a cool hack in one of many Black Hat programs or within the Arsenal lounge AND attempt to use mentioned hack on the convention itself. That’s clearly a ‘no-no’ and, in lots of instances, very unlawful. If issues go too far, we are going to take the suitable motion.
A helpful Cisco XDR Automate workflow, deployed by Adi Sankar and up to date by Abhishek Sha (as talked about in a put up above), helps streamline our menace looking efforts through a Webex plugin that feeds alerts into our collaboration platform, considerably bettering menace response occasions. Do you’ve got a number of product person interfaces and menace intelligence sources to log-in to? Integration and enhancing intelligence supply helps ease the overhead of combing by mountains of information.
Making use of this plug-in to our NOC menace looking duties, we have been capable of rapidly establish a tool that was beaconing out to a number of identified malicious websites.
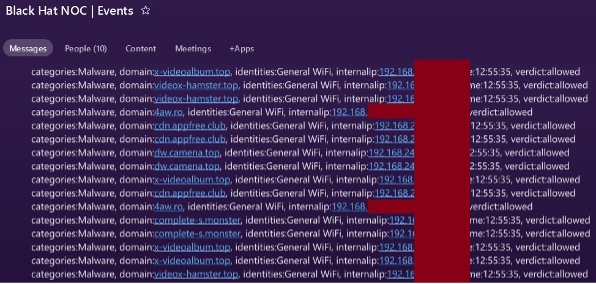
After additional investigation and looking DNS data for *hamster*, we discovered that one other person was slightly distracted on their system throughout the convention. You can even see beneath how we permit Coaching rooms to hook up with new (and probably malicious) domains for academic functions.
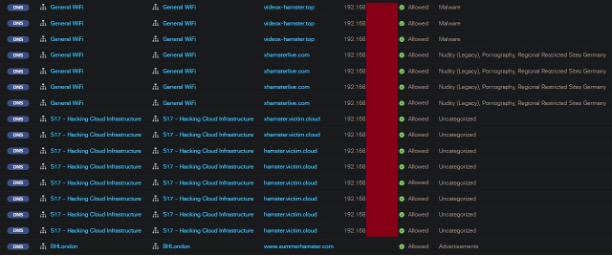
Digging into the difficulty of the person repeatedly connecting to a number of identified malicious websites, utilizing yet one more visibility enhancement we made at Black Hat Singapore 2023, we recognized every community zone the person traversed throughout the present. Once more, if this have been a company surroundings and an actual menace was recognized, this information may very well be used to zero on particular compromised units, giving the community crew a map of easy methods to reply and probably quarantine within the occasion a menace has unfold. We are able to even use this to assist decide “Affected person Zero,” or the origin of the compromise itself.
 *Fast reminder: We mapped out each Black Hat community zone on the ExCel middle in Umbrella to assist us establish what areas of the present flooring requests originated from.
*Fast reminder: We mapped out each Black Hat community zone on the ExCel middle in Umbrella to assist us establish what areas of the present flooring requests originated from.
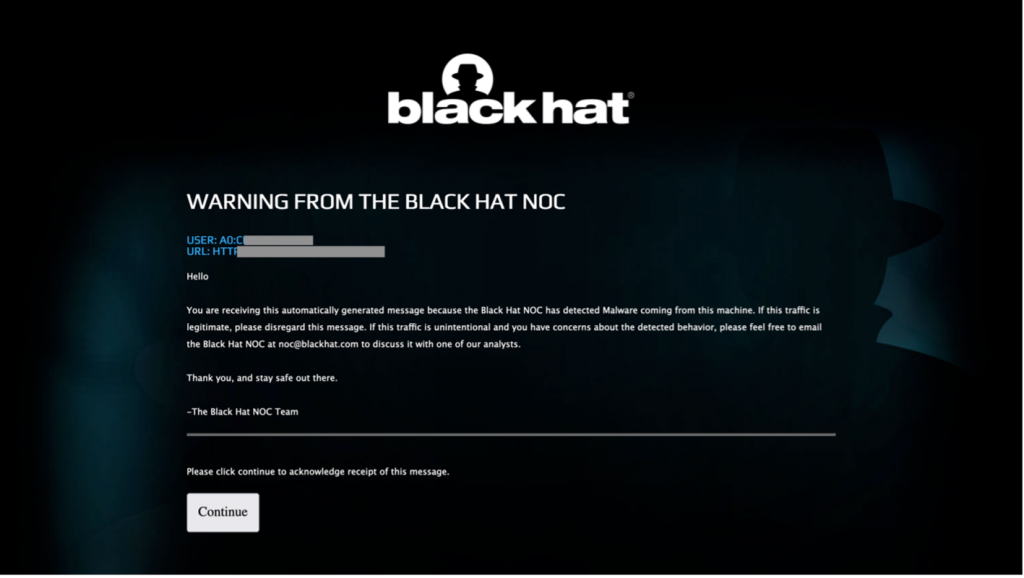
Going even deeper, utilizing Cisco Safe Cloud Analytics, we discovered the system to seemingly be an iPhone. With this new data in hand, it’s a protected assumption that the system was already compromised earlier than the attendee walked within the constructing. The NOC leaders licensed Palo Alto Networks to place up a captive portal to warn the person that the machine was contaminated.
As I discussed above, Umbrella would usually block these identified malicious requests and porn visits (in case your community admin deemed needed) in the actual world, proper off the bat. Right here at Black Hat nevertheless, as a result of this can be a studying surroundings, we usually permit all requests. To assist educate and serve the convention attendees higher, moderately than kicking them off the community, we give them notification through a captive portal. If the attendee disregards our warning (comparable to conducting illegal actions), we are going to once more take the suitable motion.
All in all, we’re very happy with the collaborative efforts made right here at Black Hat Europe by each the Cisco crew and all of the taking part distributors within the NOC. Nice work everyone!

Black Hat Asia might be in April 2024, on the Marina Bay Sands, Singapore…hope to see you there!
Acknowledgments
Thanks to the Cisco NOC crew:
- Cisco Safety: Ivan Berlinson, Abhishek Sha, Alejo Calaoagan, Adam Kilgore and Alicia Garcia Sastre
- Meraki Programs Supervisor: Paul Fidler and Connor Loughlin
- Further Assist and Experience: Adi Sankar, Ryan Maclennan, Robert Harris, Jordan Chapian, Junsong Zhao, Vadim Ivlev and Ajit Thyagarajan

Additionally, to our NOC companions NetWitness (particularly David Glover, Iain Davidson and Alessandro Zatti), Palo Alto Networks (particularly James Holland), Corelight (particularly Dustin Lee), Arista Networks (particularly Jonathan Smith), and the whole Black Hat / Informa Tech employees (particularly Grifter ‘Neil Wyler’, Bart Stump, Steve Fink, James Pope, Michael Spicer, Jess Stafford and Steve Oldenbourg).

About Black Hat
For over 25 years, Black Hat has offered attendees with the very newest in data safety analysis, improvement, and tendencies. These high-profile international occasions and trainings are pushed by the wants of the safety neighborhood, striving to deliver collectively the perfect minds within the business. Black Hat evokes professionals in any respect profession ranges, encouraging progress and collaboration amongst academia, world-class researchers, and leaders in the private and non-private sectors. Black Hat Briefings and Trainings are held yearly in the US, Europe and USA. Extra data is on the market at: Black Hat.com. Black Hat is delivered to you by Informa Tech.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Related with Cisco Safety on social!
Cisco Safety Social Channels
Share:
