Let’s say that, in the course of the center of a busy day, you obtain what appears to be like like a work-related e mail with a QR code. The e-mail claims to come back from a coworker, requesting your assist in reviewing a doc. You scan the QR code together with your telephone and it takes you to what appears to be like like a Microsoft 365 sign-in web page. You enter your credentials; nevertheless, nothing appears to load.
Not considering a lot of it, and being a busy day, you proceed to go about your work. A pair minutes later a notification buzzes your telephone. Not selecting it up instantly, one other notification comes. Then one other, and one other after that.
Questioning what’s occurring, you seize the telephone to discover a collection of multi-factor authentication (MFA) notifications. You had simply tried to log into Microsoft 365, possibly there was a delay in receiving the MFA notification? You approve one and return to the Microsoft 365 web page. The web page nonetheless hasn’t loaded, so that you get again to work and resolve to examine it later.
That is similar to an assault that Cisco Talos Intelligence discusses of their newest Talos Incident Response (IR) Quarterly Report. On this case the Microsoft 365 sign-in web page was pretend, arrange by risk actors. These attackers used compromised credentials to repeatedly try to register to the corporate’s actual Microsoft 365 web page, triggering the collection of MFA notifications—an assault method referred to as MFA exhaustion. In the long run, some workers who have been focused authorized the MFA requests and the attackers gained entry to those accounts.
Greater than the annoyance of fixing your password
Whereas the usage of QR codes is a comparatively current growth in phishing, assaults just like the one described by Talos have been round for years. Most phishing assaults make use of comparable social engineering strategies to trick customers into turning over their credentials. Phishing is often one of many high technique of gaining preliminary entry within the Talos Incident Response Quarterly Report.
Attackers hammering MFA-protected accounts can be a regarding growth within the id risk panorama. However sadly, most profitable credential compromise assaults happen with accounts that don’t have MFA enabled.
In response to this quarter’s Talos IR report, utilizing compromised credentials on legitimate accounts was one in every of two high preliminary entry vectors. This aligns with findings from Verizon’s 2023 Information Breach Investigations Report, the place the usage of compromised credentials was the highest first-stage assault (preliminary entry) in 44.7% of breaches.
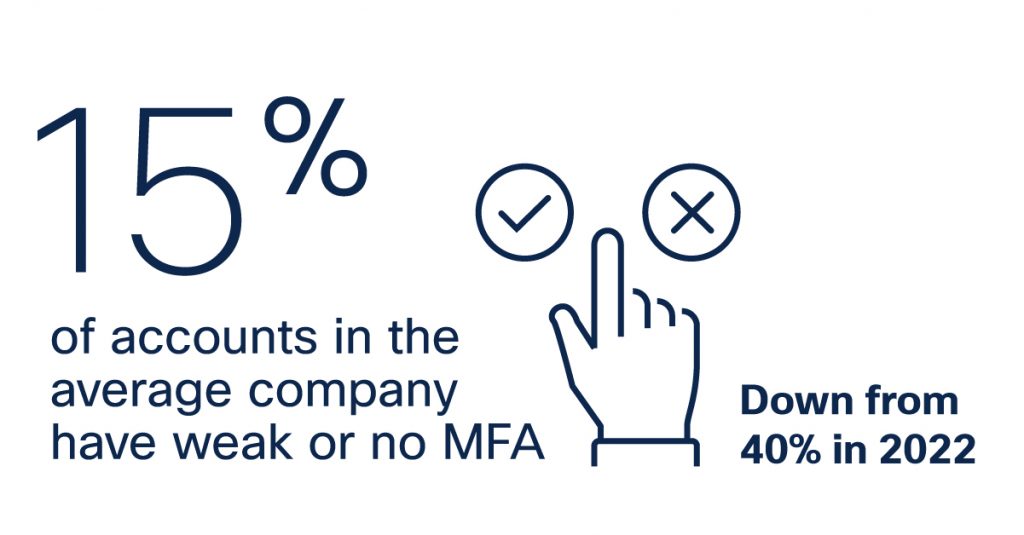
The silver lining is that this seems to be enhancing. Early final 12 months, in analysis revealed by Oort1, now part of Cisco, discovered that 40% of accounts within the common firm had weak or no MFA within the second half of 2022. up to date telemetry from February 2024, this quantity has dropped considerably to fifteen%. The change has so much to do with wider understanding of id safety, but in addition a rise in consciousness due to an uptick in assaults which have focused accounts counting on base credentials alone for cover.
How credentials are compromised
Phishing, whereas some of the standard strategies, isn’t the one method that attackers collect compromised credentials. Attackers usually try to brute pressure or password spraying assaults, deploying keyloggers, or dumping credentials.
These are only a few of the strategies that risk actors use to collect credentials. For a extra elaborate clarification, Talos lately revealed a wonderful breakdown of how credentials are stolen and utilized by risk actors that’s value looking at.
Not all credentials are created equal
Why would possibly an attacker, who has already gained entry to a pc, try to realize new credentials? Merely put, not all credentials are created equal.
Whereas an attacker can acquire a foothold in a community utilizing an odd consumer account, it’s unlikely they’ll be capable of additional their assaults because of restricted permissions. It’s like having a key that unlocks one door, the place what you’re actually after is the skeleton key that unlocks all of the doorways.
That skeleton key could be a high-level entry account reminiscent of an administrator or system consumer. Focusing on directors is sensible as a result of their elevated privileges permit an attacker extra management of a system. And goal them they do. In response to Cisco’s telemetry, administrator accounts see 3 times as many failed logins as a daily consumer account.
One other useful resource risk actors goal is credentials for accounts which might be now not in use. These dormant accounts are usually legacy accounts for older methods, accounts for former customers that haven’t been cleared from the listing, or short-term accounts which might be now not wanted. Generally the accounts can embody greater than one of many above choices, and even embody administrative privileges.

Dormant accounts are an often-overlooked safety situation. In response to Cisco’s telemetry, 39% of the whole identities inside the common group have had no exercise inside the final 30 days. It is a 60% enhance from 2022.
Visitor accounts are an account kind that repeatedly will get ignored. Whereas a handy possibility for short-term, restricted entry, these usually password-free accounts are often left enabled lengthy after they’re wanted.
And their use is rising. In February 2024, virtually 11% of identities examined are visitor accounts— representing a 233% bounce from the three% reported in 2022. Whereas we are able to solely speculate, it’s doable that cloud-adoption and distant work contributed to this rise, as enterprises used short-term accounts to stage new providers and functions or allow distant workloads within the short-term. The usage of short-term accounts is comprehensible, but when they’re forgotten or ignored, these shortcuts symbolize a critical danger.

Lowering the influence of compromised credentials
It goes with out saying that defending credentials from being compromised and abused is essential. Nonetheless, eradicating this risk is difficult.
The most effective methods to defend in opposition to these assaults is through the use of MFA. Merely confirming {that a} consumer is who they are saying they’re—by checking on one other machine or communication kind—can go a great distance in the direction of stopping compromised credentials from getting used.
Duo MFA, now accessible as a part of Cisco Consumer Safety Suite, supplies sturdy safety that’s versatile for customers, however inflexible in opposition to the usage of compromised credentials. The interface supplies a easy and quick, non-disruptive authentication expertise, serving to customers focus their time on what issues most.
MFA isn’t a silver bullet
Little doubt, deploying MFA will help in stop compromised credential abuse. Nonetheless, it isn’t a silver bullet. There are just a few ways in which risk actors can sidestep MFA.
Some MFA varieties, reminiscent of people who use SMS, could be manipulated by risk actors. In these circumstances—often known as Adversary within the Center (AitM) assaults—the attacker intercepts the MFA SMS, both via social engineering or by compromising the cell machine. The attacker can then enter the MFA SMS when prompted and acquire entry to the focused account.
The excellent news right here is that there was a drop in the usage of SMS as a second issue. In 2022, 20% of logins leveraged SMS-based authentication. As of February 2024, this quantity has declined 66%, to only 6.6% of authentications. That could be a super change, and a optimistic one at that. Along with AitM assaults, SIM swapping assaults have all however rendered SMS-based authentication checks ineffective.
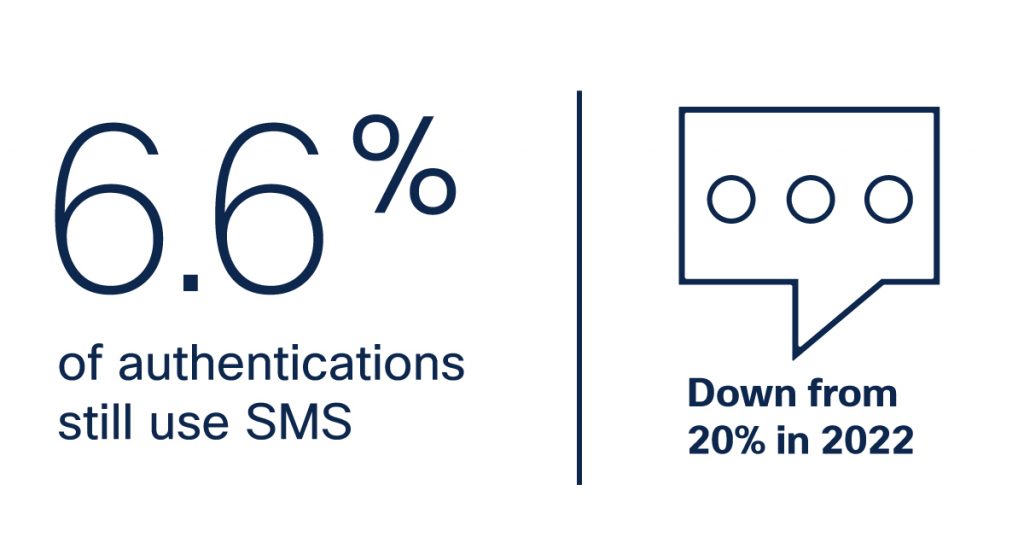
That is backed up by analysis coming from the 2024 Duo Trusted Entry Report, the place utilizing SMS texts and telephone calls as a second issue has dropped to 4.9% of authentications, in comparison with 22% in 2022.
Going passwordless
If you happen to actually wish to scale back your reliance on passwords when confirming credentials, another choice is Duo’s passwordless authentication. Passwordless authentication is a gaggle of id verification strategies that don’t depend on passwords in any respect. Biometrics, safety keys, and passcodes from authenticator apps can all be used for passwordless authentication.
Primarily based on the numbers, passwordless is the brand new pattern. In 2022, phishing resistant authentication strategies reminiscent of passwordless accounted for lower than 2% of logins. Nonetheless, in 2024, Cisco’s telemetry exhibits this quantity is climbing, at the moment representing 20%, or practically a 10x enhance. That is nice information, however nonetheless highlights a vital level—80% are nonetheless not utilizing robust MFA.

Defending MFA from risk actors
Recall the MFA exhaustion assault Talos described of their newest IR report.
Talos’ instance does spotlight how there are choose circumstances the place attackers can nonetheless get previous MFA. A distracted or annoyed consumer might merely settle for a notification simply to silence the applying. On this case, consumer training can go a great distance in the direction of stopping these assaults from succeeding, however there may be extra that may be finished.
Cisco has lately launched the first-of-its-kind Cisco Identification Intelligence to assist shield in opposition to identity-based assaults like these. This groundbreaking know-how can detect uncommon id patterns, based mostly on conduct, when mixed with Duo.
As an example, let’s take a look at when the risk actor begins hammering the login with the compromised credentials. Identification Intelligence can acknowledge anomalies reminiscent of MFA floods, in addition to the second the consumer will get irritated and accepts the request.
It could actually additionally pinpoint anomalies reminiscent of a consumer signing in from an unmanaged machine in a location that might be not possible for them to succeed in—say Peculiar, Missouri—given that they had simply logged in an hour in the past from Regular, Illinois.

Cisco Identification Intelligence will instantly handle the visibility hole between authenticated identities and trusted entry by a data-driven and AI-first method. Cisco Identification Intelligence is a multi-sourced, vendor agnostic, investment-preserving resolution that works throughout the prevailing id stack and brings collectively authentication and entry insights to ship a really robust safety protection.
Cisco clients desirous about signing up for the general public preview can fill out a request to affix at the moment.
We’d love to listen to what you suppose. Ask a Query, Remark Under, and Keep Linked with Cisco Safety on social!
Cisco Safety Social Channels
Share:
