Safety researchers have noticed Purple Hat and Ubuntu techniques being attacked by a Linux model of the DinodasRAT (often known as XDealer) which will have been working since 2022.
The Linux variant of the malware has not been described publicly, though the primary model has been tracked to 2021.
Cybersecurity firm ESET has beforehand seen DinodasRAT compromising Home windows techniques in an espionage marketing campaign dubbed ‘Operation Jacana,’ that focused authorities entities.
Earlier this month, Pattern Micro reported a couple of Chinese language APT group they monitor as ‘Earth Krahang,’ which used XDealer to breach each Home windows and Linux techniques of governments worldwide.
DinodasRAT particulars
In a report earlier this week, researchers at Kaspersky say that when executed, the Linux variant of DinodasRAT creates a hidden file within the listing the place its binary resides, which acts as a mutex to stop a number of cases from working on the contaminated system.
Subsequent, the malware units persistence on the pc utilizing SystemV or SystemD startup scripts. To complicate detection, the malware then executes as soon as extra whereas the father or mother course of waits.
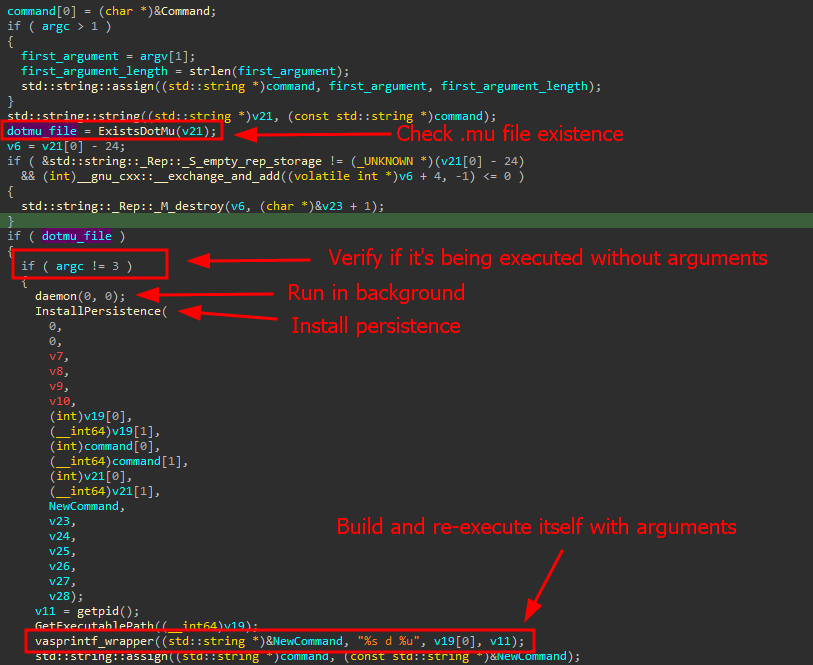
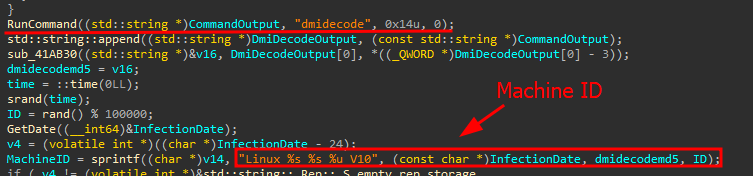
The contaminated machine is tagged utilizing an infection, {hardware}, and system particulars and the report is distributed to the command and management (C2) server to handle sufferer hosts.
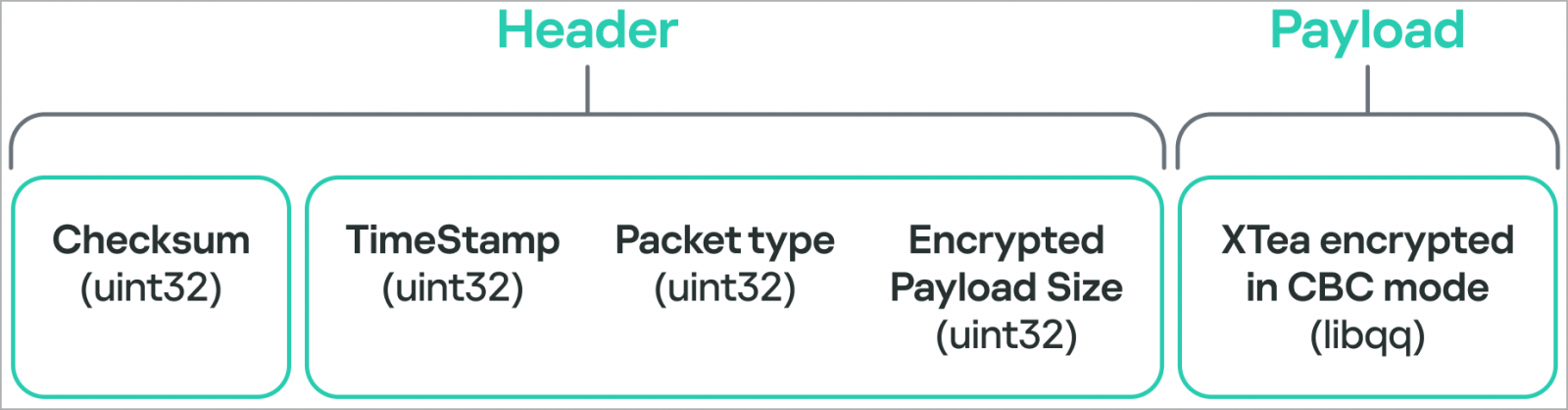
Communication with the C2 server happens by way of TCP or UDP, whereas the malware makes use of the Tiny Encryption Algorithm (TEA) in CBC mode, guaranteeing secured information trade.
DinodasRAT has capabilities designed to watch, management, and exfiltrate information from compromised techniques. Its predominant options embody:
- Monitor and harvest information on person actions, system configurations, and working processes.
- Obtain instructions for execution from the C2, together with file and listing actions, shell command execution, and updating the C2 handle.
- Enumerate, begin, cease, and handle processes and providers on the contaminated system.
- Provide the attackers a distant shell for direct command or file execution in separate threats.
- Proxy C2 communications by distant servers.
- Obtain new variations of the malware that doubtlessly incorporate enhancements and extra capabilities.
- Uninstall itself and wipe all traces of its earlier exercise from the system.
In line with the researchers, DinodasRAT offers the attacker full management over compromised techniques. They be aware that the risk actor is utilizing the malware primarily to achieve and preserve entry to the goal by Linux servers.
“The backdoor is totally purposeful, granting the operator full management over the contaminated machine, enabling information exfiltration and espionage,” Kaspersky says.
Kaspersky doesn’t present particulars in regards to the preliminary an infection technique however notes that since October 2023 the malware impacts victims in China, Taiwan, Turkey and Uzbekistan.
